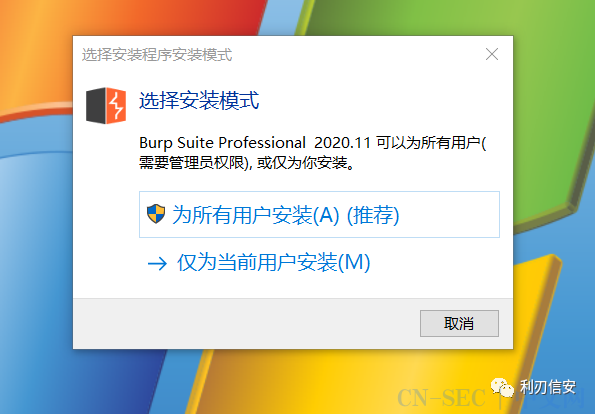
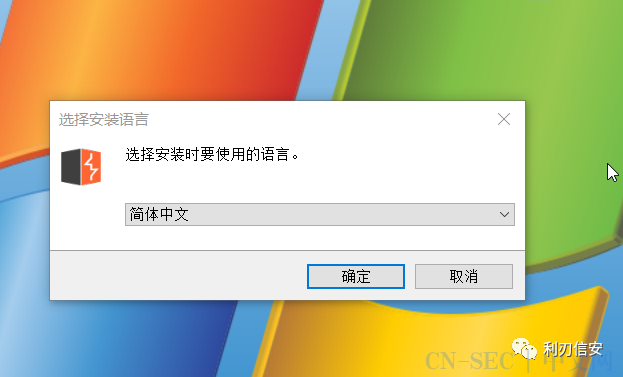
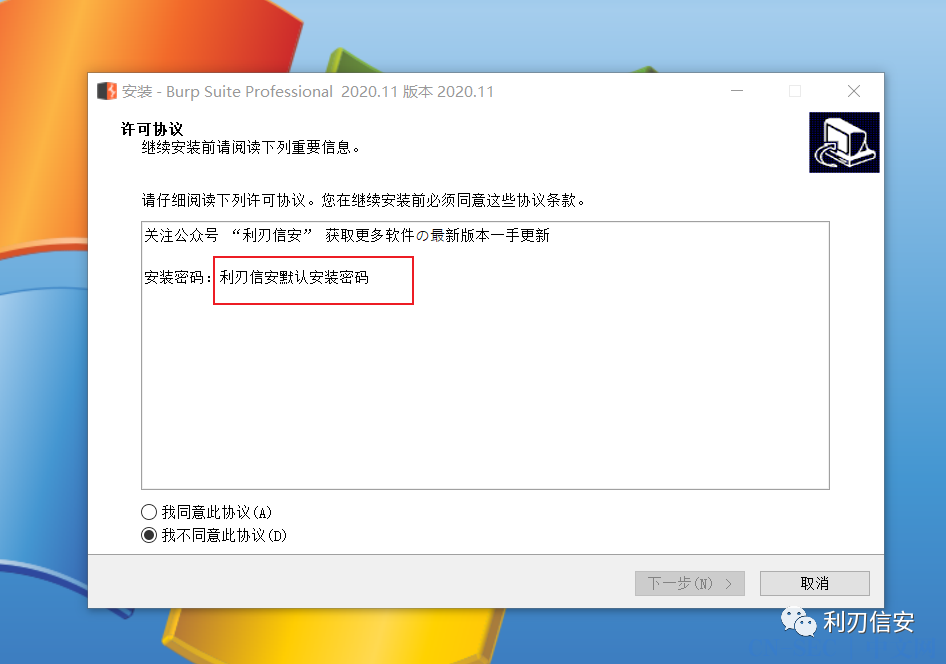
Burp Suite Professional 2020.11【微信公众号首发,禁止转载】,资源存活时间8小时
Burp Suite是一款信息安全从业人员必备的集 成型的渗透测试工具,它采用自动测试和半自动测试的方式,包含了 Proxy,Spider,Scanner,Intruder,Repeater,Sequencer,Decoder,Comparer等工具模块。通 过拦截HTTP/HTTPS的web数据包,充当浏览器和相关应用程序的中间人,进行拦截、修改、重放数据包进行测试,是web安全人员的一把必备的瑞士军刀。
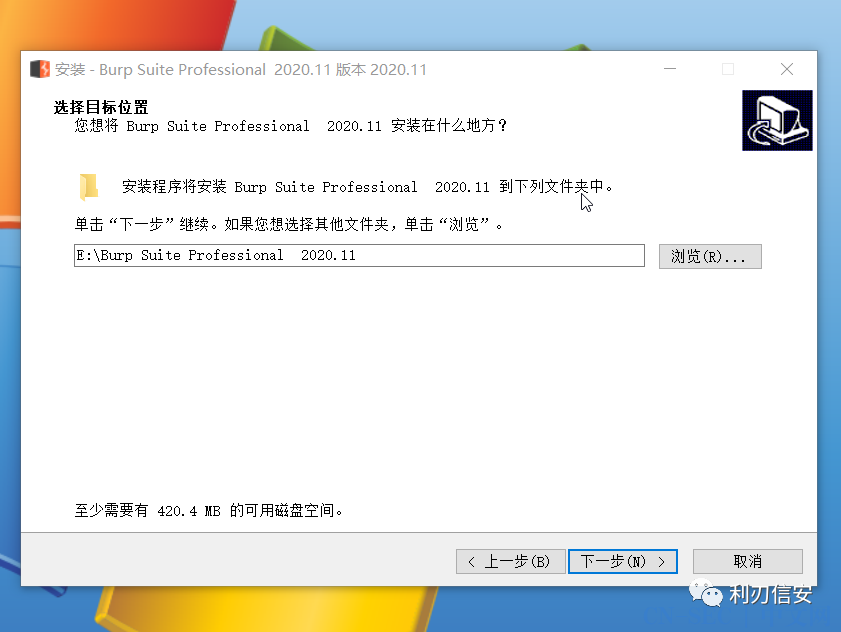
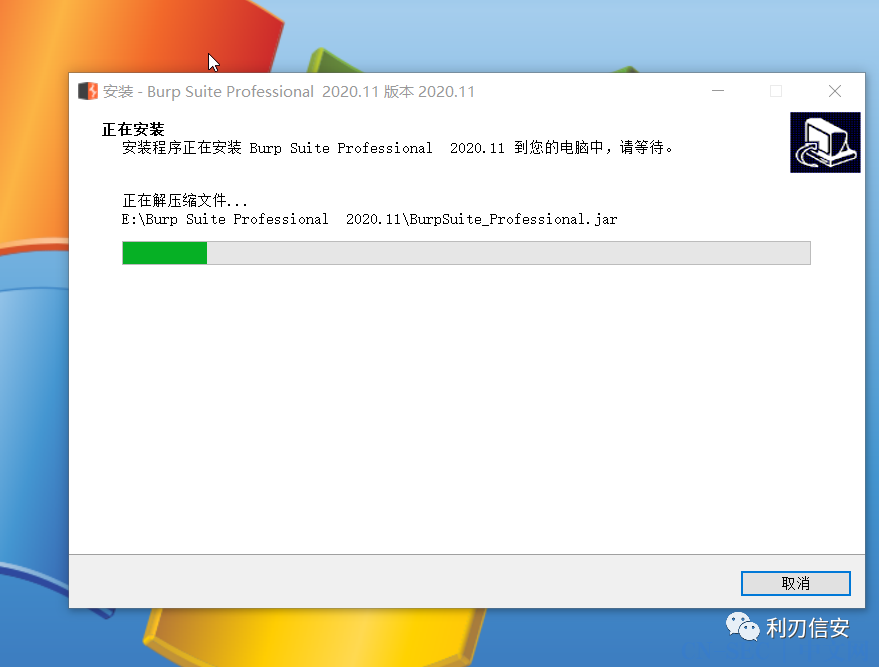
File Size: 165MB
Burp Suite is a reliable and practical platform that provides you with a simple means of performing security testing of web applications. It gives you full control, letting you combine advanced manual techniques with various tools that seamlessly work together to support the entire testing process. The utility is easy-to-use and intuitive and does not require you to perform advanced actions in order to analyze, scan and exploit web apps. It is highly configurable and comes with useful features to assist experienced testers with their work.
The main window displays all the available tools you can choose from and set each one’s settings the way you want.
Being designed to work alongside your browser, the application functions as an HTTP proxy, thus all the HTTP/s traffic from your browser passes through the utility. This way, if you want to perform any kind of testing, you need to configure the browser to work with it.
The first thing you need to do is to confirm that the app’s proxy listener is active. Simply navigate to the Proxy tab and take a look in the Proxy Listeners section. You should see an entry in the table with the Running check box ticked. The second thing you are required to do is to configure your browser to use the app’s proxy listener as its HTTP proxy server. Finally, you need to configure the browser to be able to send HTTP requests through the app without problems.
The previously mentioned utility gives you complete control over all of the actions you want to perform and get detailed information and analysis about the web applications you are testing. Using tools such as Intruder, Repeater, Sequencer and Comparer you are able to carry out different actions with ease.
With the help of Spider, you can crawl an application to locate its content and functionality. You are able to add new scope by selecting the protocol and specifying the host name or the IP range. Then the utility monitors all the transferred bytes and queued requests.
The Intruder tool enables you to perform attacks against web apps. Simply set the host name and the port number, define one or more payload sets and you are done. You can also use the HTTP protocol by checking the proper box from the Target tab.
Another tool that automates testing tasks is called Sequencer, which analyzes the quality of randomness in an application’s session tokens. Firstly, you need to load at least 100 tokens, then capture all the requests.
Overall, Burp Suite Free Edition lets you achieve everything you need, in a smart way. It helps you record, analyze or replay your web requests while you are browsing a web application.
Features of Professional Edition:
- Burp Proxy
- Burp Spider
- Burp Repeater
- Burp Sequencer
- Burp Decoder
- Burp Comparer
- Burp Intruder
- Burp Scanner
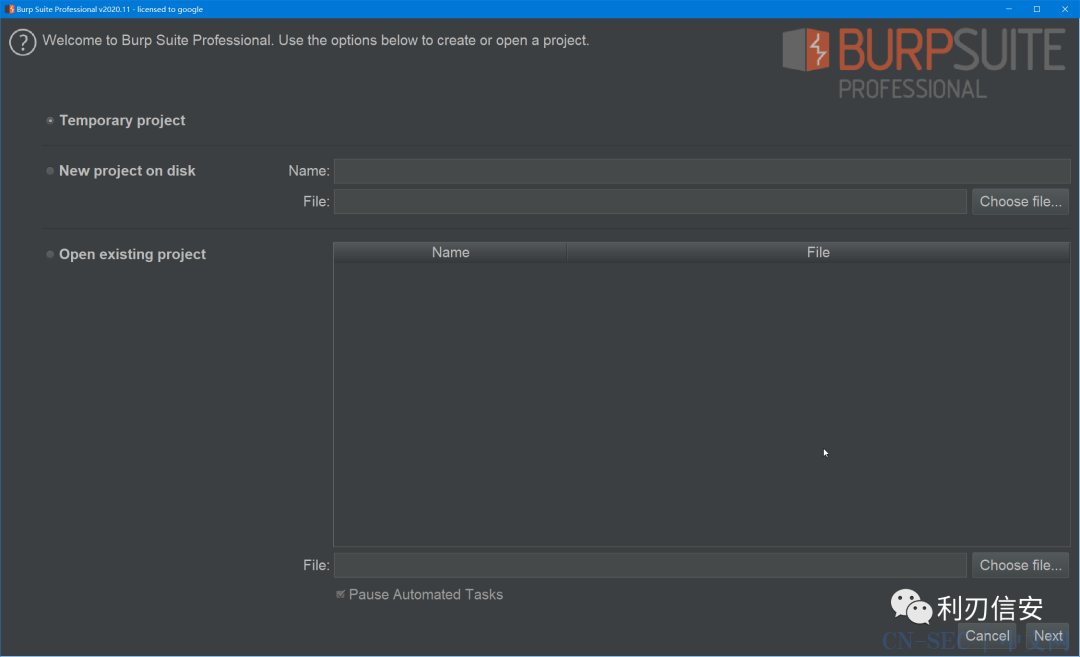
- Save and Restore
- Search
- Target Analyzer
- Content Discovery
- Task Scheduler
- Release Schedule
Homepage
https://portswigger.net
This release provides several new features for both manual and automated testing, as well as some major upgrades to the message editor UI.
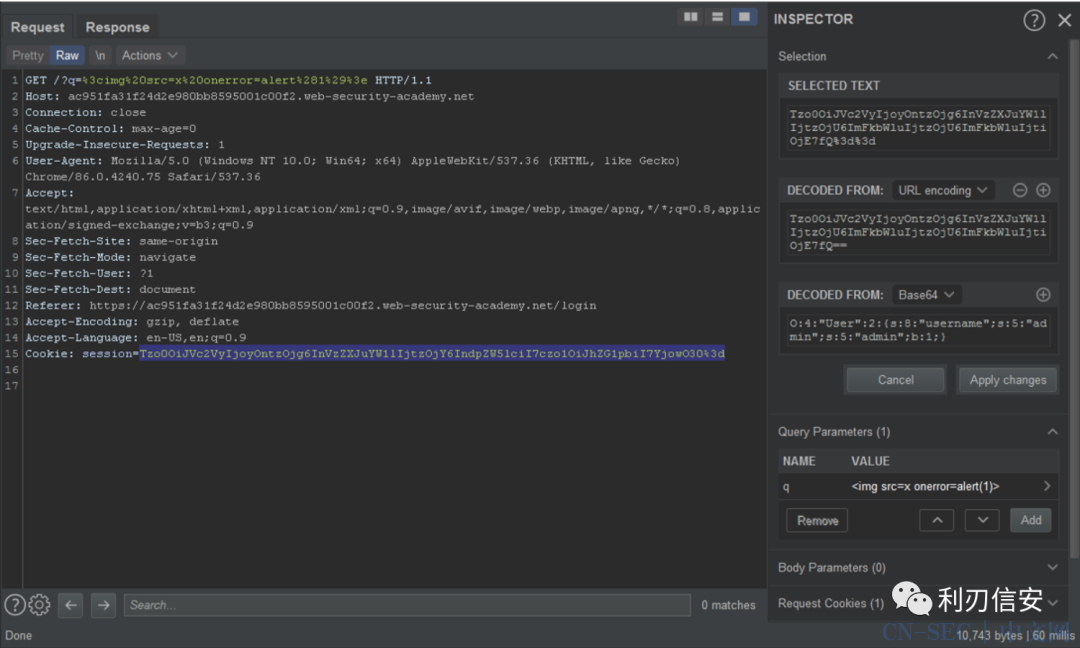
Message inspector
The new message inspector is a collapsible panel displayed on the right-hand side of the message editor throughout Burp Suite. It provides a quick way to analyze and work with interesting features of HTTP and WebSocket messages without having to switch between different tabs.
The Hex, Params, Headers, and Cookies tabs that used to appear in the message editor have been removed. You can now access the same functionality, and some additional new features, directly in the inspector panel.
-
Perform basic operations such as viewing and manipulating any headers, parameters, and cookies found in HTTP messages. You can also add new ones to the request.
-
Instantly decode HTML, URL, and Base64-encoded values. The inspector automatically applies the appropriate sequence of transformations to decode headers, parameters, cookies, and any encoded text that you manually select in a message.
-
Work with encoded data more easily by editing it in its decoded form. The inspector automatically reapplies the necessary encodings as you type so that you can inject your modified value into the request with a single click or key press.
-
Inject non-printing characters by modifying the code point of a character.
You perform some of these actions by drilling down into items that were automatically identified by the inspector. Alternatively, you can manually select one or more characters in a message to work with them in the inspector panel.
For more information about using the inspector, please refer to the documentation.
API scanning
Burp Scanner is now able to scan both JSON and YAML-based APIs for vulnerabilities. By default, the crawler attempts to parse any API definitions that it encounters to identify potential endpoints, along with their supported methods and parameters. You can also explicitly provide the URL of an API definition when launching a scan. Based on the endpoints that it discovers, Burp Scanner is then able to derive new locations to crawl and audit.
If you prefer, you can disable API scanning by deselecting the "Parse API definitions" crawl option in your scan configuration. You can find this option under "Miscellaneous".
Please note that this initial release only supports scanning of a fairly limited range of REST APIs. For a full list of the prerequisites and limitations, please refer to the documentation. We plan to further develop this feature and gradually add support for a wider range of APIs in future releases.
Test recorded login sequences
In the previous release, we added new functionality for recording and uploading full login sequences to help Burp Scanner handle more complex authentication mechanisms. This release adds a new feature that allows you to replay your recorded login sequences in an embedded browser.
This makes it much easier to check whether the recording accurately captured your browser interactions. It may also help you to diagnose any problems if the login sequence is failing during scans.
For more information, please refer to the documentation.
Automatic updates
By default, Burp now automatically downloads any available updates. When a new update has been downloaded, a notification will prompt you to restart Burp in order to install it. Note that you will still need to download the 2020.11 release manually.
If you prefer, you can disable automatic updates in the user options.
Other improvements
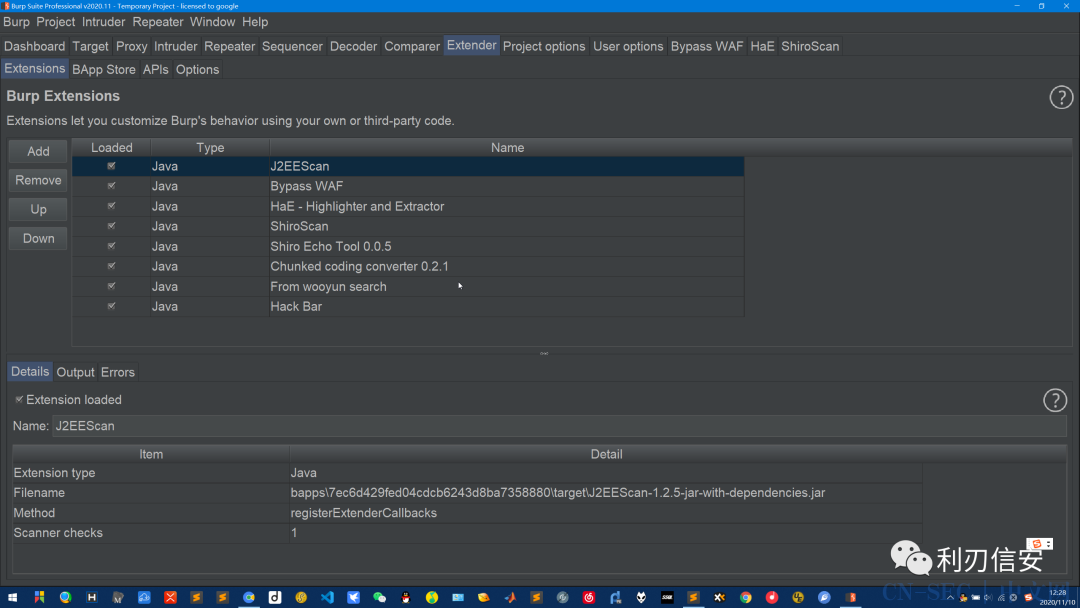
To help reduce clutter, the custom views that some Burp extensions add to the message editor are no longer accessed via individual tabs. Instead, you can now alternate between your extension-specific views using a new drop-down menu.
Bug fixes
-
We have fixed a bug that was causing the Burp UI to freeze in specific circumstances when the .NET Beautifier extension was enabled.
-
When hovering the mouse over a long, encoded token in an HTTP message, the decoded text no longer overflows the tooltip. We have also extended the tooltip so that it can display up to 2000 characters.
-
Launching an installed version of Burp now provides the same range of character sets as when launching Burp from a JAR file.
下载地址:
https://lrxa.herokuapp.com/
本文始发于微信公众号(利刃信安):Burp Suite Professional 2020.11【微信公众号首发,禁止转载】,资源存活时间8小时
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论