#1 漏洞代码
/grad/admin/domain_logo.php
[php]
/**修改:王磊
*修改时间:2007-04-09
*修改内容:判断域LOGO的路径
*
*/
$domain = $_COOKIE['cookie'];//接收cookie值,无任何过滤
$fp = popen("/var/eyou/sbin/hashid ".$domain,'r');//直接带进了危险函数popen 执行任意命令
$res = fread($fp,1024);
header('Content-type:image/rgb');
$path = "/var/eyou/Domain/".substr($res,-5,2).$domain."/LOGO/domain_logo";
$fp = file($path);
foreach($fp as $key => $val){
print($val);
}
exit;
?>
[/php]
[php]
$domain = $_COOKIE['cookie'];
//接收cookie值,无任何过滤
$fp = popen("/var/eyou/sbin/hashid ".$domain,'r');
//直接带进了危险函数popen 可远程执行任意命令
[/php]
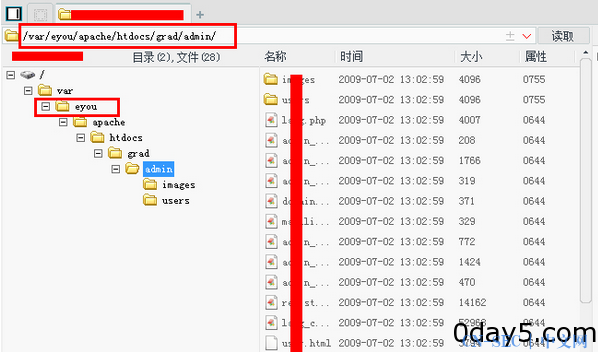
#2 漏洞利用
访问http://secmap.cn/grad/admin/domain_logo.php
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论