漏洞作者: Power
shop/join.php中
if($action=="postnew") { //自定义字段的合法检查与数据处理 $Module_db->checkpost($field_db,$postdb,'');//跟踪 join_post(); unset($id_array);checkpost()函数中
function checkpost($field_db,&$postdb,$rsdb=''){ foreach($field_db AS $key=>$rs) { .................省略 else { if(is_array($postdb[$key])){ $postdb[$key]='/#/'.implode("/#/",$postdb[$key]).'/#/'; } //过滤不安全的字符 $postdb[$key]=filtrate($postdb[$key]);//对传递过来的数据进行过滤 } if(strlen($postdb[$key])>30000){ showerr("内容不能大于1.5万个汉字"); } } }上面的我无法利用,但是在shop//member/address.php中
elseif($action=="postnew"){ $db->query("INSERT INTO `{$_pre}address` (`uid` ,`order_username` ,`order_phone` ,`order_mobphone` ,`order_email` ,`order_qq` ,`order_postcode` ,`order_address` ) VALUES ('$lfjuid', '$order_username', '$order_phone', '$order_mobphone', '$order_email', '$order_qq', '$order_postcode', '$order_address')");//直接转义之后入库 refreshto("?job=list",'',0); }elseif($action=="edit"){ checkrid($rid); $db->query("UPDATE `{$_pre}address` SET order_username='$order_username',order_phone='$order_phone',order_email='$order_email',order_qq='$order_qq',order_postcode='$order_postcode',order_address='$order_address',order_mobphone='$order_mobphone' WHERE rid='$rid'");//转移后入库 refreshto("?job=list",'',0); }在shop/join.php中
if($action=="postnew") { //自定义字段的合法检查与数据处理 $Module_db->checkpost($field_db,$postdb,''); join_post();//跟踪join_post()函数中
function join_post(){ extract($GLOBALS); global $postdb,$listdb; if(!table_field("{$_pre}join",'products')){ $db->query("ALTER TABLE `{$_pre}join` ADD `products` TEXT NOT NULL ;"); } $query = $db->query("SELECT * FROM {$_pre}content WHERE id IN (".implode(',',$_ar).")"); while($rs = $db->fetch_array($query)){ $rs[price] = str_replace(',','',$rs[price]); $listdb[$rs[uid]][] = $rs; /* var_dump($listdb); exit; */ } if($postdb[address_type]>0){ $ts = $db->get_one("SELECT * FROM `{$_pre}address` WHERE uid='$lfjuid' AND rid='$postdb[address_type]'"); //数据出库 $postdb[order_username] = $ts[order_username]; $postdb[order_phone] = $ts[order_phone]; $postdb[order_mobphone] = $ts[order_mobphone]; $postdb[order_email] = $ts[order_email]; $postdb[order_qq] = $ts[order_qq]; $postdb[order_postcode] = $ts[order_postcode]; $postdb[order_address] = $ts[order_address]; }elseif($postdb[address_type]=='-1'){ $db->query("INSERT INTO `{$_pre}address` ( `uid` , `order_username` , `order_phone` , `order_mobphone` , `order_email` , `order_qq` , `order_postcode` , `order_address` ) VALUES ('$lfjuid' , '$postdb[order_username]' , '$postdb[order_phone]' , '$postdb[order_mobphone]' , '$postdb[order_email]' , '$postdb[order_qq]' , '$postdb[order_postcode]' , '$postdb[order_address]')"); } }/shop/join.php中
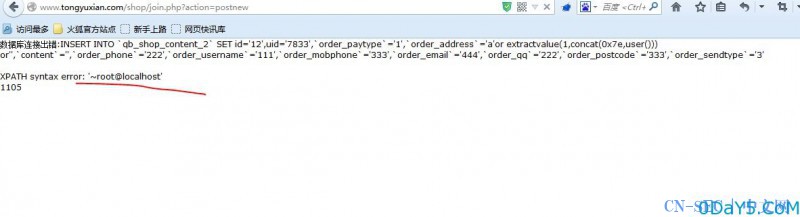
if($action=="postnew") { //自定义字段的合法检查与数据处理 $Module_db->checkpost($field_db,$postdb,''); join_post();//此函数取出入库数据 unset($id_array); foreach($listdb AS $uid=>$array){ $totalmoney = 0; $detail=''; foreach($array AS $_rs){ $totalmoney+=$_rs[price]*$p_totalArray[$_rs[id]]; $detail[] = "$_rs[id]={$p_totalArray[$_rs[id]]}"; } $products = addslashes( implode(',',$detail) ); $rs=$db->get_one("SELECT * FROM `{$pre}purse` WHERE uid='$uid'"); $parray=unserialize($rs[config]); if($postdb[order_sendtype]==2){ //平邮 $totalmoney+=floatval($parray[slow_send]); }elseif($postdb[order_sendtype]==3){ //快递 $totalmoney+=floatval($parray[norm_send]); }elseif($postdb[order_sendtype]==4){ //EMS $totalmoney+=floatval($parray[ems_send]); } //$totalmoney = number_format($totalmoney,2); /*往主信息表插入内容*/ $db->query("INSERT INTO `{$_pre}join` ( `mid` , `cid` , `cuid` , `posttime` , `uid` , `username` , `yz` , `ip` , `totalmoney`,`products`) VALUES ( '$mid' , '$_rs[id]' , '$uid', '$timestamp','$lfjdb[uid]','$lfjdb[username]','0','$onlineip','$totalmoney','$products')"); $id = $id_array[] = $db->insert_id(); unset($sqldb); $sqldb[]="id='$id'"; $sqldb[]="uid='$lfjuid'"; /*检查判断辅信息表要插入哪些字段的内容*/ foreach( $field_db AS $key=>$value){ isset($postdb[$key]) && $sqldb[]="`{$key}`='{$postdb[$key]}'"; } $sql=implode(",",$sqldb); $db->query("INSERT INTO `{$_pre}content_$mid` SET $sql");//数据入库产生注入漏洞证明:
估计是我的Mysql 注册版本太低,不能报错注入,http://www.tongyuxian.com/shop/此网站躺抢
首先注册一个个人用户,访问http://www.tongyuxian.com/shop//member/address.php?job=postnew
然后购买商品,结算,使用存在的地址。
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-





评论